Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Showing: 401 to 425 of 940Affiliation shown is the affiliation at the time the talk was given.
Protecting a billion identities without losing (much) sleep
Mark Crosbie, Tim Tickel, Four Flynn - Facebook
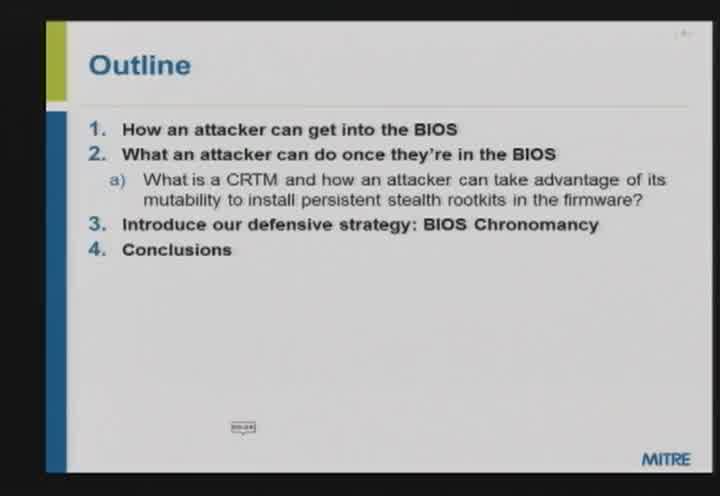
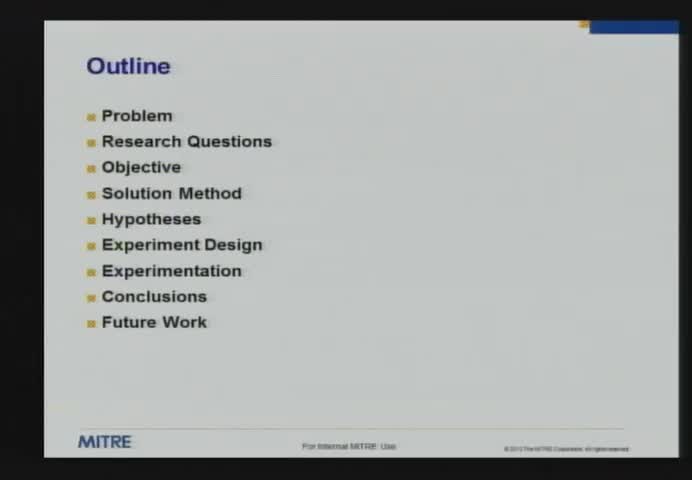
BIOS Chronomancy: Using Timing-Based Attestation to Detect Firmware Rootkits
John Butterworth - MITRE
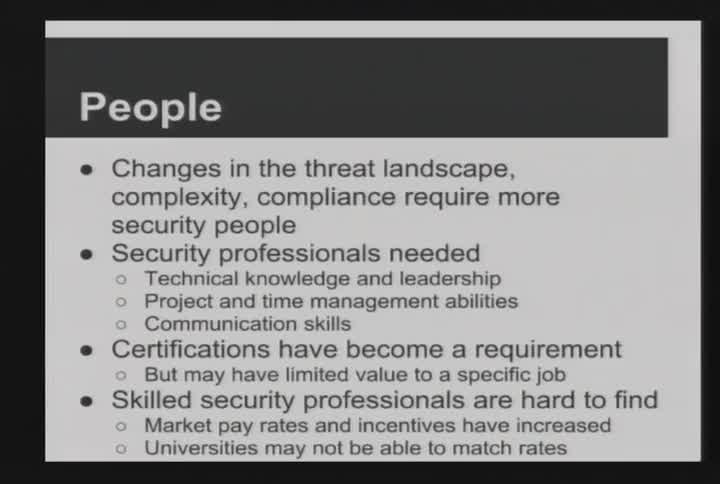
Information Security Challenges in an Academic Environment
Keith Watson - Purdue University
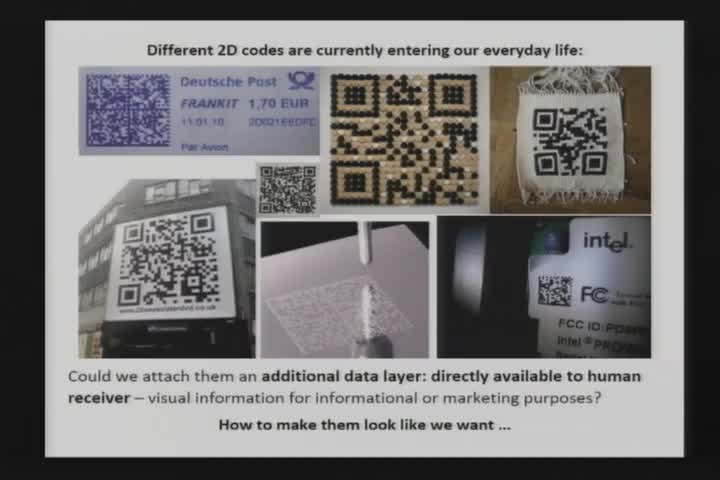
New possibilities of steganography based on Kuznetsov-Tsybakov problem
Jarek Duda - Purdue University
Towards Automated Problem Inference from Trouble Tickets
Rahul Potharaju - Purdue University
The Growing Role--and Problems--Facing Science and Engineering
Norman R. Augustine - Lockheed Martin Corporation (Retired)
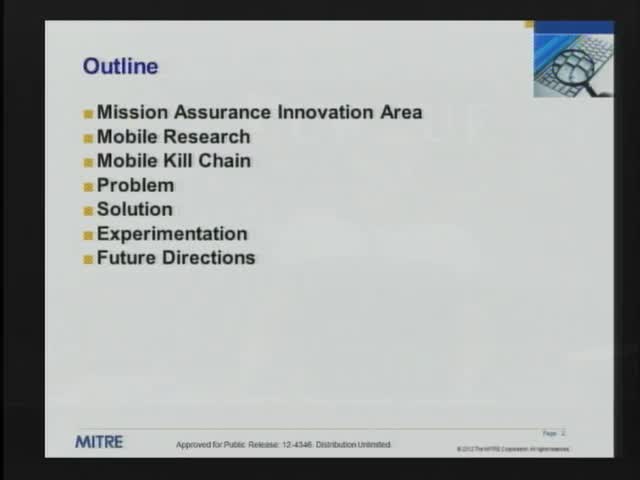
Active Cyber Network Defense with Denial and Deception
Kristin Heckman - MITRE
Whole Genome Sequencing: Innovation Dream or Privacy Nightmare?
Emiliano DeCristofaro - PARC
Protecting Today's Enterprise Systems against Zero-day Attacks
Saurabh Bagchi - Purdue University
Minimizing Private Data Disclosures in the Smart Grid
Weining Yang - Purdue University
I'm not stealing, I'm merely borrowing - Plagiarism in Smartphone App Markets
Rahul Potharaju - Purdue University
Using Probabilistic Generative Models for Ranking Risks of Android Apps
Chris Gates - Purdue University
A Semantic Baseline for Spam Filtering
Christian F. Hempelmann - Texas A&M University-Commerce
Differentially Private Publishing of Geospatial Data
Wahbeh Qardaji - Purdue University
Automatic Detection of Protocol Manipulation Attacks in Distributed Systems Implementations
Cristina Nita-Rotaru - Purdue University
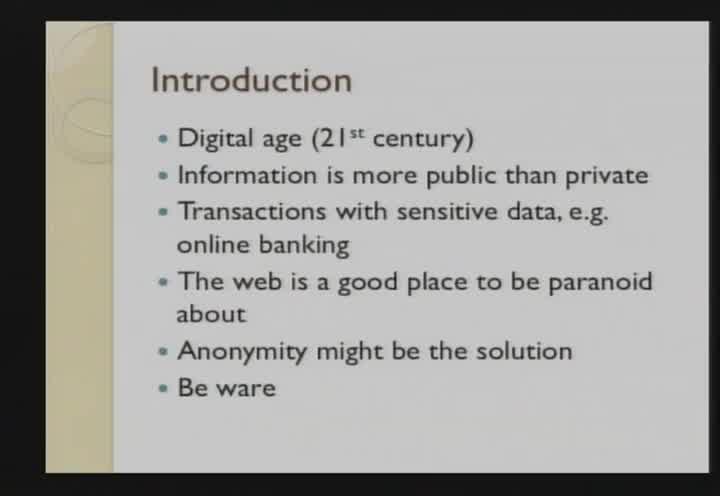
You are Anonymous!!! Then you must be Lucky
Bilal Shebaro - Purdue University
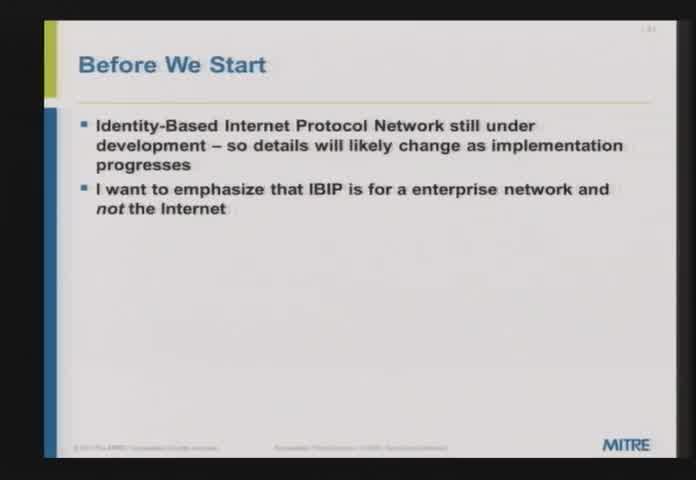
Not the Who but the What -- New applications of Hardware Identity
Hal Aldridge - Sypris
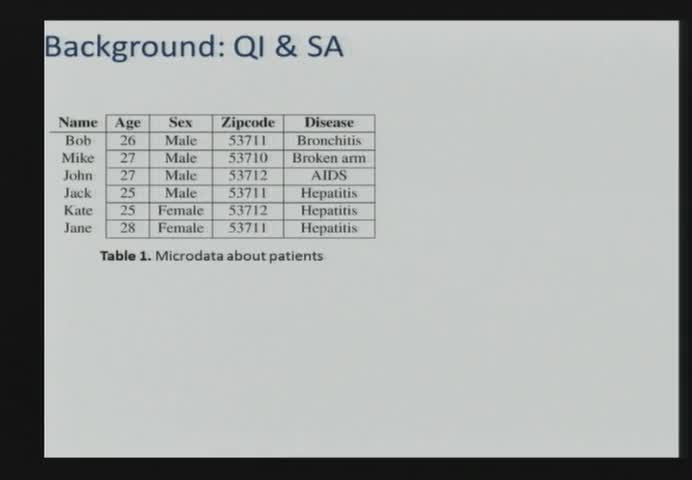
Publishing Microdata with a Robust Privacy Guarantee
Jianneng Cao - Purdue University
Risk perception of information security risks online
Vaibhav Garg - Indiana University
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List