Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Showing: 551 to 575 of 940Affiliation shown is the affiliation at the time the talk was given.
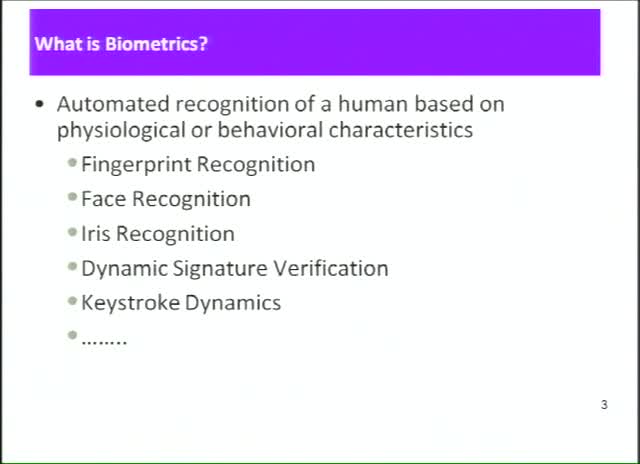
Fingerprint Sensor Interoperability: Analysis of Error Rates for Fingerprint Datasets Acquired from Multiple Fingerprint Sensors
Shimon Modi - Purdue University
Virtualization: Resource Coupling and Security across the Stack
Dennis Moreau - Configuresoft
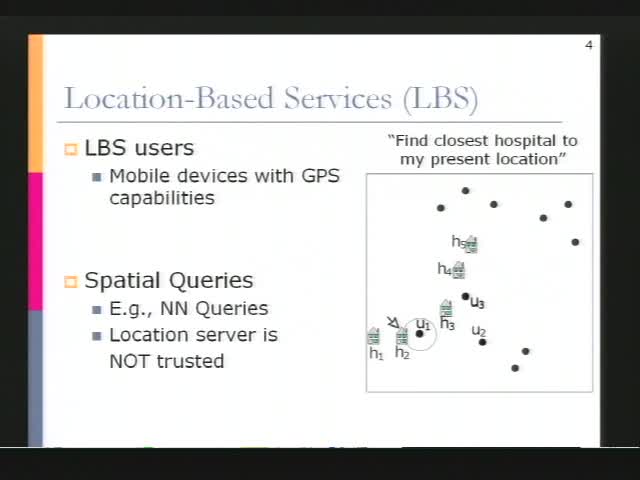
Private Queries in Location Based Services: Anonymizers are not Necessary
Gabriel Ghinita - Purdue University
Exploitable Redirects on the Web: Identification, Prevalence, and Defense
Minaxi Gupta - Indiana University
Shifting focus: Aligning security with risk management
Jack Jones - Risk Management Insight
Exploiting Opportunistic Scheduling in Cellular Data Networks
Hao Chen - University of California, Davis
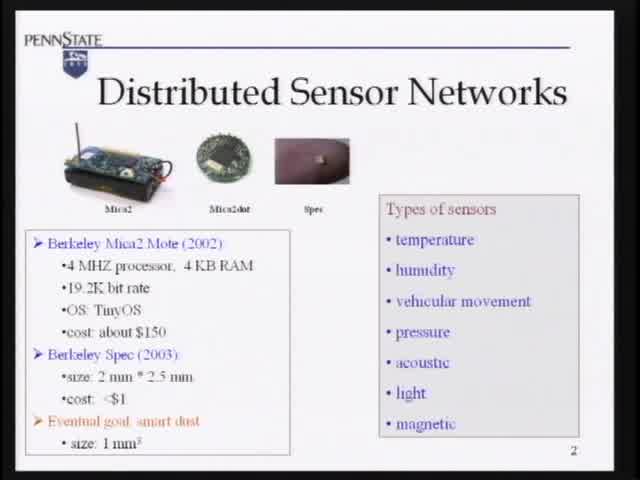
Towards Event Source Location Privacy in Wireless Sensor Networks
Sencun Zhu - Pennsylvania State
Multiple Independent Levels of Security Architecture: A High Robustness Approach Using COTS
Ben Calloni - Lockheed Martin
Reading the Disclosures with New Eyes: Bridging the Gap between Information Security Disclosures and Incidents
Ta-Wei "David" Wang - Purdue University
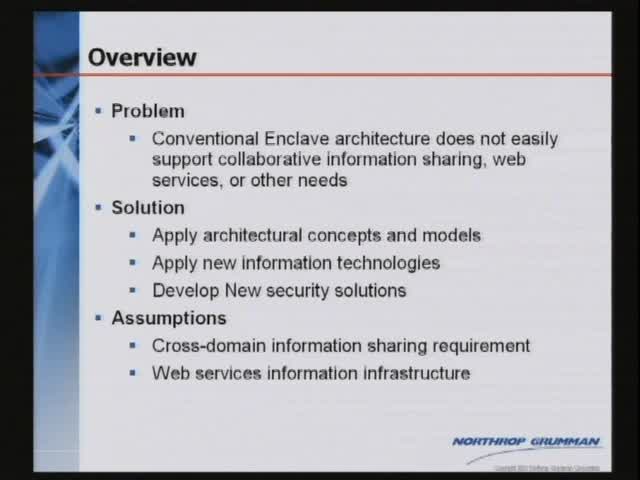
Beyond the Enclave: Evolving Concepts in Security Architectures
Myron Cramer - Essex
What are CSO's thinking about? Top information security initiatives for 2008 and beyond …
Anand Singh - Target Corporation
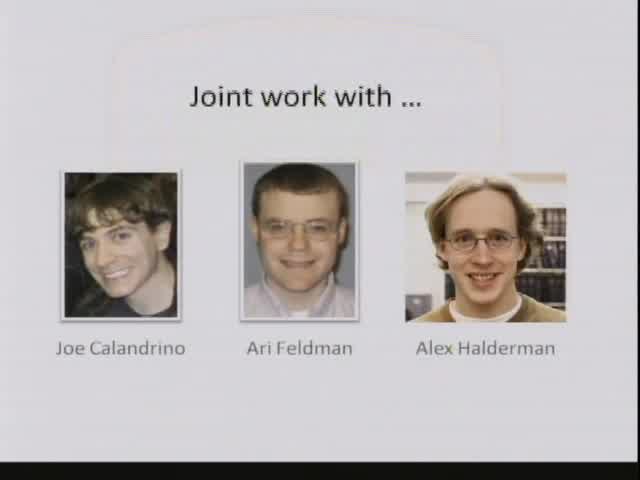
Electronic Voting: Danger and Opportunity
Edward W. Felten - Princeton University
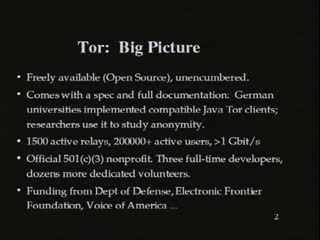
Tor: Anonymous communications for government agencies, corporations, journalists... and you
Paul Syverson & Roger Dingledine - U.S. Naval Research Laboratory (NRL)
CANDID: Preventing SQL Injection Attacks using Dynamic Candidate Evaluations
Ventkat Venkatakrishnan - University of Illinois at Chicago
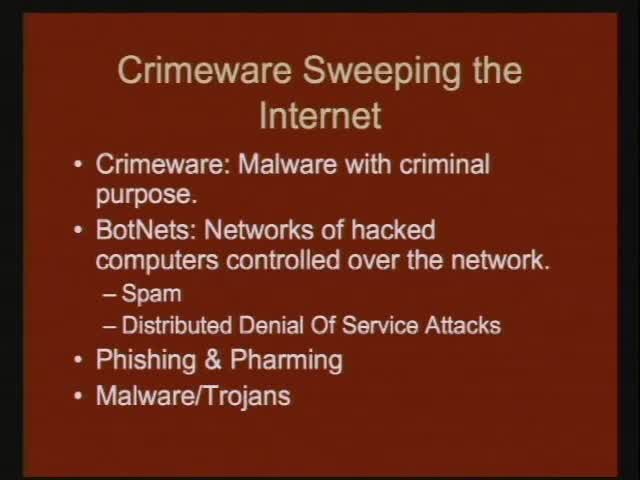
Wireless Router Insecurity: The Next Crimeware Epidemic
Steve Myers, Indiana University - Indiana University

Security, Soft Boundaries, and oh-so-subtle Strategies:How to Play Chess While the Board is Disappearing
Richard Thieme - ThiemeWorks
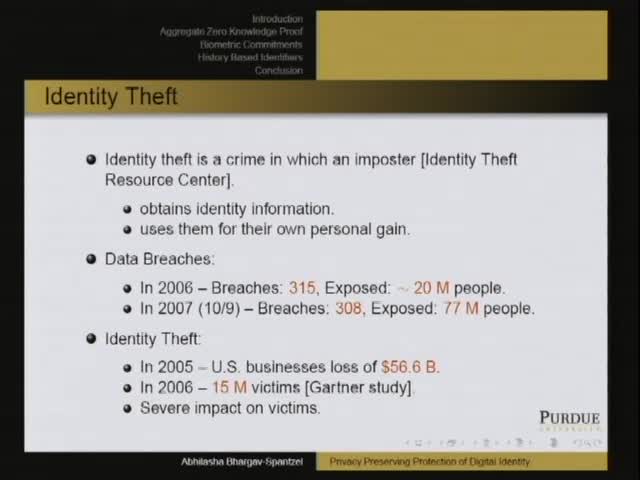
Protocols and Systems for Privacy Preserving Protection of Digital Identity
Abhilasha Bhargav-Spantzel - Purdue University
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List