Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Showing: 301 to 325 of 940Affiliation shown is the affiliation at the time the talk was given.
When Side Channel Meets Row Hammer: Cache-Memory Attacks in Clouds and Mobile Devices
Yinqian Zhang - The Ohio State University

The Application of Natural Language Processing to Open Source Intelligence for Ontology Development in the Advanced Persistent Threat Domain
Corey Holzer - Purdue University
A Science of Cyber Infrastructure Configuration
Sanjai Narain - Vencore Labs
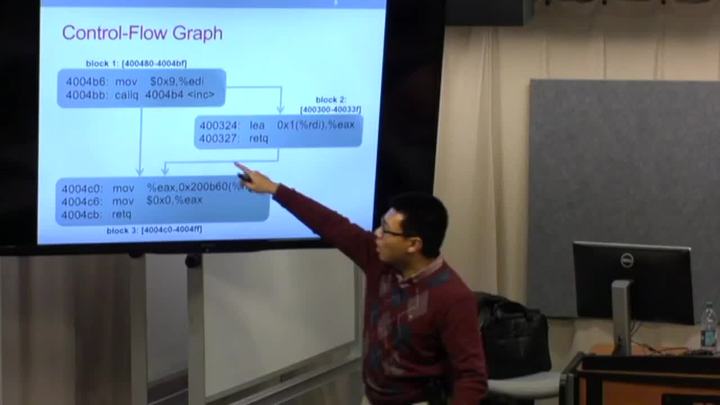
Protecting Computer Systems by Eliminating Vulnerabilities
Byoungyoung Lee - Purdue University
New Research and Resources in NL IAS at Purdue
Victor Raskin - Purdue University
Enforcing Least Privilege Memory Views for Multithreaded Applications
Terry Ching-Hsiang Hsu - Purdue University
Growing Up In Cyber, But Is Cyber Growing Up?
Tony Sager - Center for Internet Security

The role of cyber insurance in security and risk management
Nicholas Reuhs - Ice Miller LLP

The Internet of Value: Privacy and Applications
Aniket Kate - Purdue University
Secure Coding - Patterns and anti-patterns in the design & architecture of secure applications
Michael Taylor - Rook Security

ErsatzPasswords - Ending Password Cracking
Christopher N. Gutierrez - Purdue University
Information Security: Through the Lens of Crisis Organizations
Kelley Misata - Purdue University
Privacy-preserving payments in credit networks
Pedro Moreno Sanchez - Purdue University

Finding Specification Noncompliance and Attacks in Wireless Network Protocol Implementations
Endadul Hoque

Bottom Line Security: Understanding the True Cost of Cybersecurity Attacks
Chris Kanich
Usable Secure Webmail for Grassroots Adoption
Kent Seamons - Brigham Young University
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List