Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Showing: 251 to 275 of 940Affiliation shown is the affiliation at the time the talk was given.

Double the Factors, Double the Fails: How Usability Obstacles Impact Adoption of Strong Authentication Habits
Jessy Irwin - Tendermint
Kernel-Supported Cost-Effective Audit Logging for Causality Tracking
Shiqing Ma - Purdue University

What's Private: Exploring Reasonable Expectation of Privacy in the Age of Modern Innovation
Jillean Long Battle - Rofori Corporation

Breaching Water Treatment Plants: Lessons Learned from Complex Exercises
Doug Rapp - Rofori Corporation

Hacking Your Security Career: Strategies That College Did Not Teach Me
Ryan Elkins - Eli Lilly

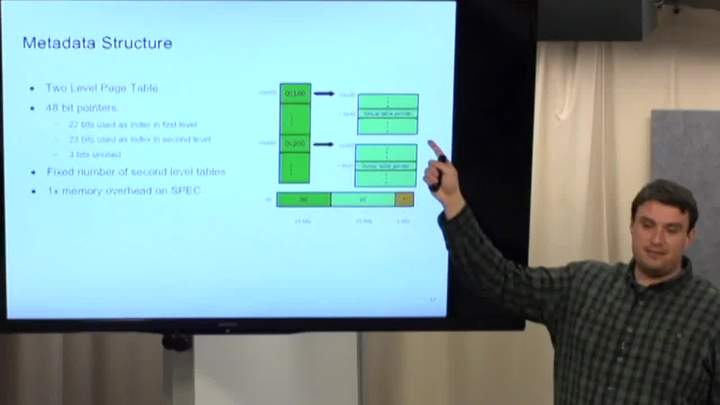
Protecting Bare-metal Embedded Systems from Memory Corruption Attacks
Abe Clements - Purdue University

Personally Identifiable Data and the Specter of Customer Privacy
Leon Ravenna - KAR Auction Services, Inc.
Anonymity Trilemma : Strong Anonymity, Low Bandwidth Overhead, Low Latency – Choose Two.
Debajyoti Das - Purdue University

Symposium Closing Keynote - Bits & Bytes, Flesh & Blood, and Adapting for the Next 20 Years
Josh Corman - PTC
Leveraging DevSecOps to Escape the Hamster Wheel of Never-ending Security Fail
Chris Reed - Eli Lilly

Mind Your Credit: Assessing the Health of the Ripple Credit Network
Pedro Moreno-Sanchez - Purdue University

Lessons Learned From the Retrocomputing Community
Mitchell Parker - IU Health
OBLIVIATE: A Data Oblivious File System for Intel SGX
Adil Ahmad - Purdue University
Eli Lilly's Path to a Successful Threat Intelligence Program
Brian Lynch - Eli Lilly
What Roles Can Empirical Research Play to Advance Software Security Knowledge?
Lotfi ben-Othmane - Iowa State University
Securing the Future of Business: Broadening the Role of Security Technology
Kirsten Bay - Cyber adAPT
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List