Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Showing: 576 to 600 of 940Affiliation shown is the affiliation at the time the talk was given.

From Securing Navigation Systems to Securing Wireless Communication
Srdjan Capkun - ETH Zurich
What Every Engineer Needs To Know About Security And Where To Learn It
Neil Daswani - Google
Do You Have My Data? Prove it! (Provable Data Possession at Untrusted Stores)
Reza Curtmola - Purdue University
The Effect of Rootkits on the Corporate Environment
David Ehinger - Rolls Royce
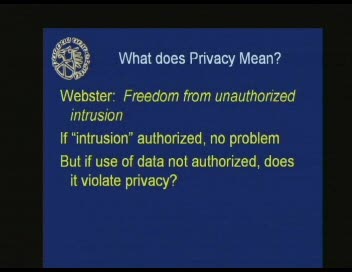
Protecting Data Privacy: A Practical Guide to Managing Risk
Jill Frisby - Crowe Chizek and Company LLC
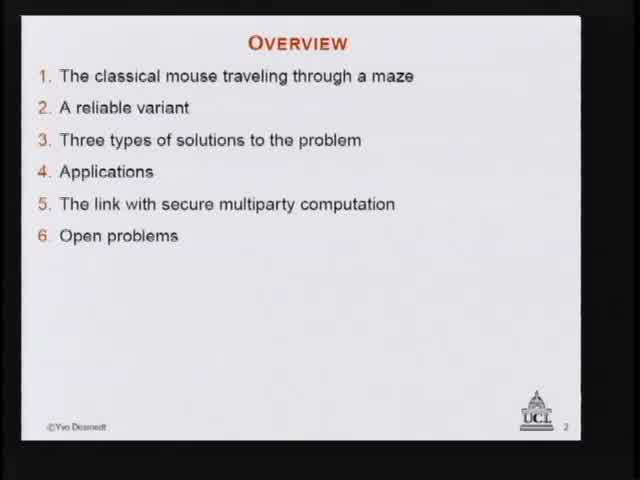
Applying Recreational Mathematics to Secure Multiparty Computation
Yvo Desmedt - University College, London
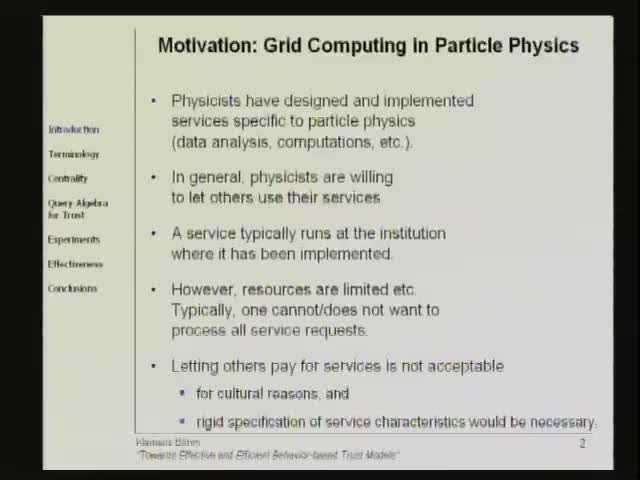
Towards Effective and Efficient Behavior-based Trust Models
Klemens Boehm - Karlsruhe University
Passwords Decay, Words Endure: Towards Secure and Re-usable Multiple Password Mnemonics
Umut Topkara - Purdue University

Hiding the Message Behind the Words: Advances in Natural Language Watermarking
Mercan Topkara - Purdue University
Dumb Ideas in Computer Security
Dr. Charles P. Pfleeger - Pfleeger Consulting Group
How the Criminal Law Must Adapt to the Networked World
Richard Downing - US Department of Justice
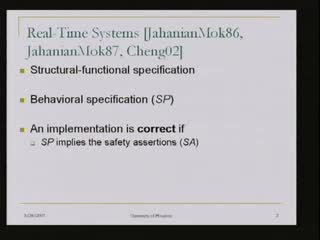
Automatic Debugging and Verification of RTL-Specified Real-Time Systems via Incremental Satisfiability Counting and On-Time and Scalable Intrusion Detection in Embedded Systems
Dr. Albert M. K. Cheng - University of Houston

Intrusion Detection Event Correlation: Approaches, Benefits and Pitfalls
Eugene Schultz - High Tower Software

Assured Information Sharing between Trustworthy, Semi-trustworthy and Untrustworthy Coalition Partners
Bhavani Thuraisingham - The University of Texas at Dallas
Cyber Security and the "NEW" world enterprise
Howard Schmidt - R & H Security Consulting LLC
Scenario-Driven Construction of Enterprise Information Policy
Stuart Shapiro - The MITRE Corporation

Computer-Related Incidents: Factors Related to Cause and Prevention
Virginia Rezmierski - University of Michigan
The Psychology of Computer Deviance: How it can assist in digital evidence analysis.
Marc Rogers - Purdue University
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List