Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Affiliation shown is the affiliation at the time the talk was given.
A Survey of intrusion detection research at the IBM Zurich Research Laboratory
Marc Dacier - IBM Global Security Laboratory
Anonymity and cryptographic protocols
Mikhail Atallah - CERIAS /Purdue CS Department
Practical Security Solutions Using Smartcards
Naomaru Itoi and James Rees - CITIUniversity of Michigan
Trends in Intrusion Detection: Perspectives from a Security Tool Vendor
Gene Kim - Tripwire Security Systems Inc.
The Windows NT Security Model & Architecture
E. Eugene Schultz - Global Integrity
Windows NT Security-Related Vulnerabilities
E. Eugene Schultz - Global Integrity
Oblivious transfer and its applications
Mikhail Atallah - CERIAS /Purdue CS Department
Forensic Analysis of Computer Compromises
Charles Boeckman - MITRE Corporation
The Evolving Corporate Public-Key Infrastructure
Anish Bhimani - Global Integrity
Effectively Managing Your E-Business Risk Profile - A Standard Approach for Assessing Risk and Protecting Corporate Stakeholders
Rick Davis - INSUREtrust.com
KHIP - A Scalable Protocol for Secure Multicast Routing
Clay Shields - Purdue CERIAS
Twelve Challenges in Information Security Research
Gene Spafford - Purdue CERIAS
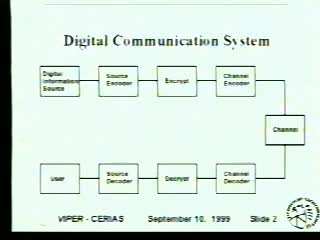
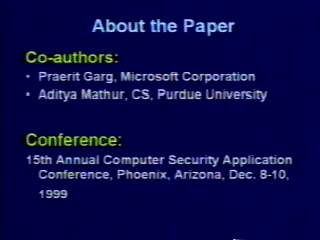
Image and Video Watermarking: An Overview
Edward J. Delp - Video and Image Processing Laboratory (VIPER), Purdue School of Electrical and Computer Engineering
Technical and legal approaches to spam
David E. Sorkin - Center for Information Technology & Privacy Law at The John Marshall Law School
Engineering secure software in Java with Confined Types
Jan Vitek - Purdue, CERIAS
Architectures and Components for High-Assurance Security
Carl Landwehr - Mitretek
A Formal Framework and Evaluation Method for Protocol Denial of Service
Catherine Meadows - Naval Research Laboratory
Anonymity Online
Albert H. Teich - American Association for the Advancement of Science

Computer Forensics Examinations in the Consulting Arena
James R. C. Hansen - Trident Data Systems
Information Security, a Folk Art in Need of an Upgrade
Donn Parker - SRI Consulting
Thwarting Denial of Service Attacks against Communication Protocols with Backward Compatible Changes: A Case Study
Mahesh Tripunitara - Purdue CERIAS
Security Relevancy Analysis on the Registry of Windows NT 4.0 (for Wenliang Du)
Wenliang Du & Mahesh Tripunitara - Purdue CERIAS
Asynchronous Transfer Mode (ATM) Networks: Security Vulnerability Research
Susan Labonte - MITRE Corporation
Developing Custom Intrusion Detection Filters Using Data Mining
Chris Clifton - The MITRE Corporation
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List