Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Showing: 526 to 550 of 940Affiliation shown is the affiliation at the time the talk was given.
Software Assurance: Motivation, Background, and Acquisition Pursuits
Joe Judge - Mitre
User Awareness of Security Countermeasures and its Impact on Information Systems Misuse: A Deterrence Approach
John D'Arcy - Notre Dame
Privacy – from accessing databases to location based services
Johann-Christoph Freytag - Humboldt University
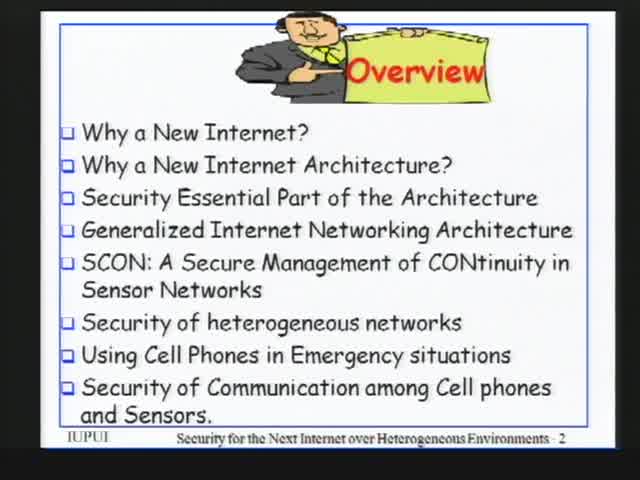
Security for the Next Internet over Heterogeneous Environments
Arjan Durresi - Indiana University Purdue University at Indianapolis

Providing Privacy through Plausibly Deniable Search
Mummoorthy Murugesan - Purdue University
Mace: Systems and Language Support for Building Correct, High-Performance Networked Services
Charles Killian - Purdue University
Quantitative Risk Assessment of Software Security and Privacy, and Risk Management with Game Theory
Mehmet Sahinoglu - Auburn University at Montgomery, AL
The Dark Side of Software Engineering and How to Defend Against It
Cassio Goldschmidt - Symantec
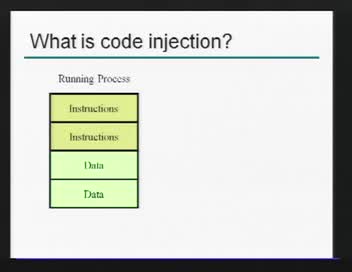
An Alternate Memory Architecture for Code Injection Prevention
Ryan Riley - Purdue University
A Rules Based Statistical Algorithm for Keystroke Detection
Paul Kidwell - Purdue University

Extending anonymity research to high-tech white collar crimes and IT Insider threat: A critical step
Ibrahim Baggili - Purdue University
Automatic Signature Generation for Unknown Vulnerabilities
Weidong Cui - Microsoft
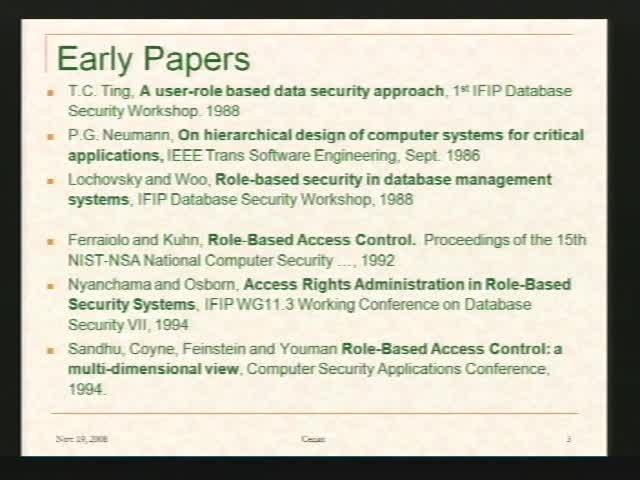
The Role Graph Model and its Extensions
Sylvia Osborn - University of Western Ontario
The "merge" of Anti-Tamper and Information Assurance - lessons learned from the Anti-Tamper discipline
Scott Orton - Ratheon
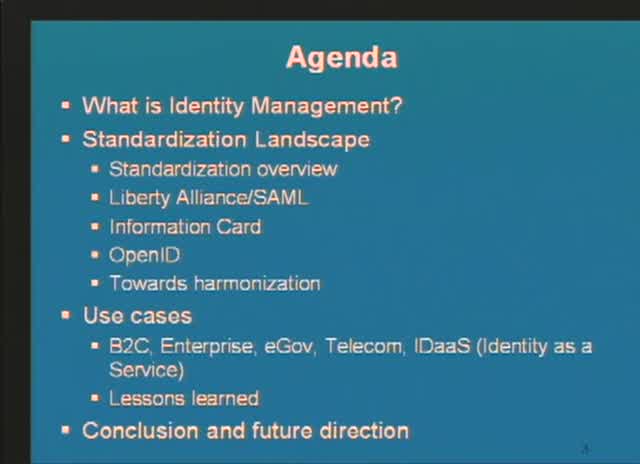
Trends in Identity Management
Kenji Takahashi - ITT Information Sharing Platform Laboratories
Signature Analysis Coupled With Slicing Analysis for the Validation of Software
Adam Dugger - Arxan
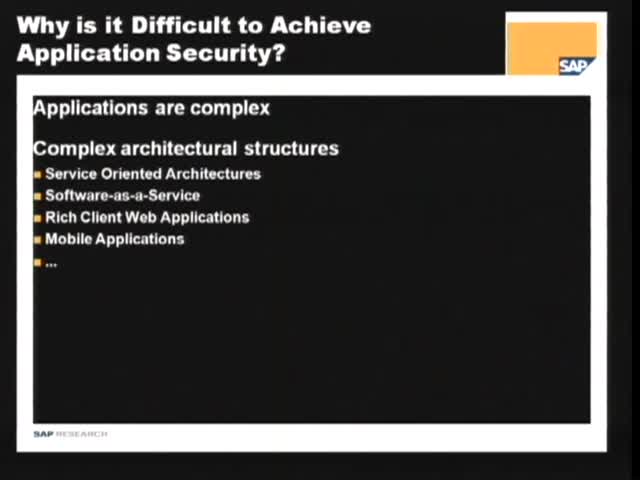
Measuring the Attack Surfaces of Enterprise Software Systems
Yuecel Karabulut - SAP Research
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List