Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Affiliation shown is the affiliation at the time the talk was given.
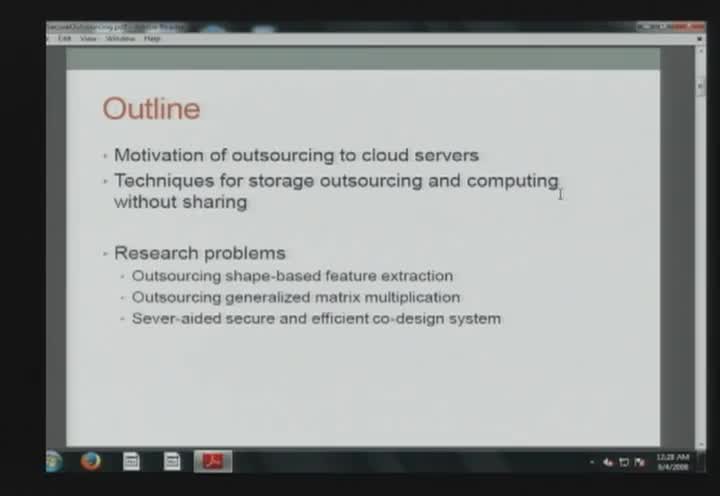
Secure and Private Outsourcing to Untrusted Cloud Servers
Shumiao Wang - Purdue University
Beehive: Large-Scale Log Analysis for Detecting Suspicious Activity in Enterprise Networks
Ting-Fang Yen - RSA
Technical Tradeoffs in the NSA's Mass Phone Call Program
Ed Felten - Princeton University
Delivering "Always-on" Services Despite Flaky Network Infrastructure
Rahul Potharaju - Purdue University
Machine Intelligence for Biometric and On-Line Security
Marina Gavrilova - University of Calgary
General-Purpose Secure Computation and Outsourcing
Marina Blanton - University of Notre Dame
Why so CERIAS!? Why we're losing and what to do about it.
Joshua Corman - Sonatype
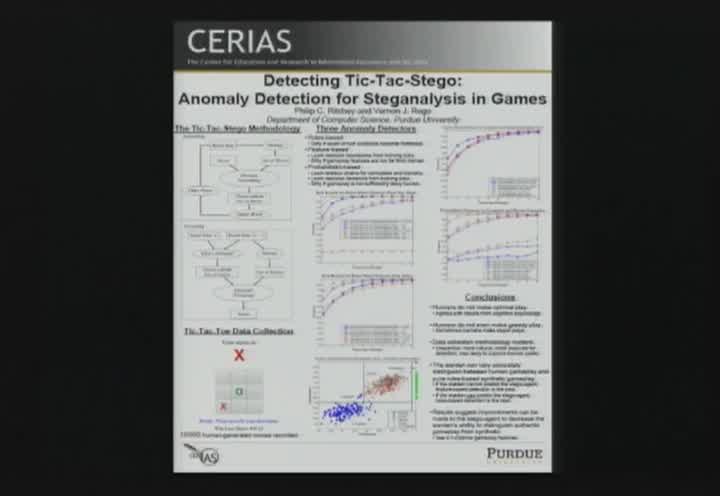
CERIAS Poster Contest Winners
Philip Ritchey & Mohammed Almeshekah - Purdue University
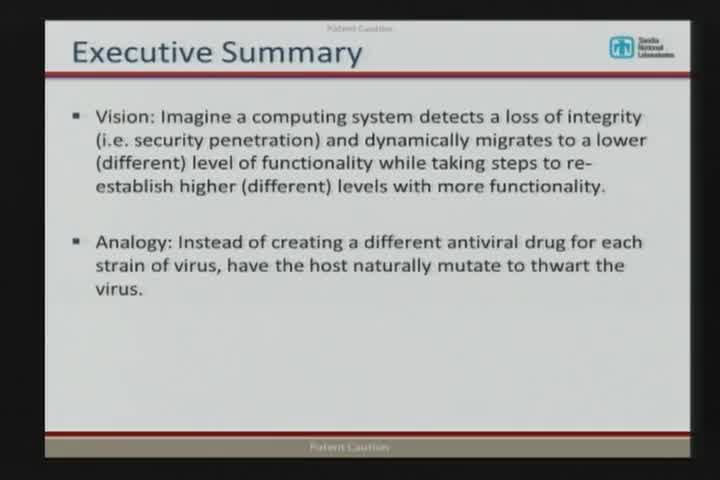
Integrity Levels: A New Paradigm for Protecting Computing Systems
Chris Jenkins - Sandia
Online Privacy Agreements, is it Informed Consent?
Masooda Bashir - University of Illinois at Urbana-Champaign
Tree-based Oblivious RAM and Applications
Elaine Shi - University of Maryland
DSCRETE: Automatic Rendering of Forensic Information from Memory Images via Application Logic Reuse
Brendan Saltaformaggio - Purdue University
WarGames in Memory: Fighting Powerful Attackers
Mathias Payer - Purdue University
Responsible Information Management and the 2014 Cost of Data Breach: Global Analysis
Larry Ponemon - Ponemon Institute

"Memory Analysis, Meet GPU Malware"
Golden G. Richard III - University of New Orleans
Healthcare Security and Privacy: Not There Yet
Robert Zimmerman - Inforistec
Improving Analyst Team Performance and Capability in NOC / SOC Operations Centers
Barrett Caldwell and Omar Eldardiry - Purdue University

You can hack, but you can't hide: Using log analysis to detect APTs
Kevin Bowers - RSA
Privacy in the Age of the Police State
Marcus Ranum - Tenable Network Security
How Program Analysis can be Used in Security Applications
Xiangyu Zhang - Purdue University
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List