Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Showing: 501 to 525 of 940Affiliation shown is the affiliation at the time the talk was given.
Detection and protection from denial of service attacks in grids by accountability agents
Wonjun Lee - Purdue University
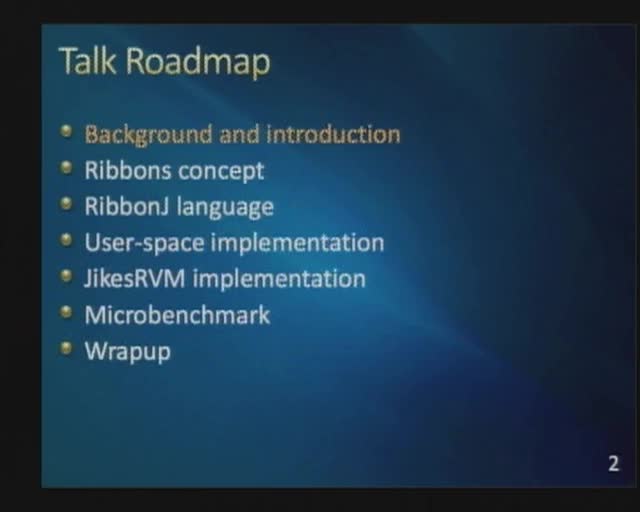
Ribbons, A Partially-Shared Memory Programming Model
Kevin Hoffman - PhD candidate in the Computer Science, Purdue University
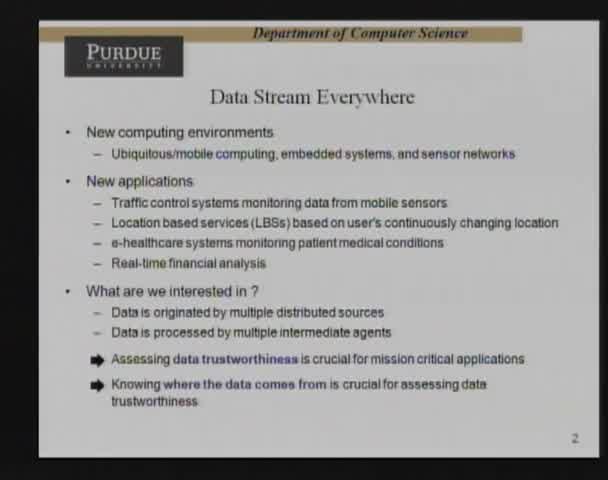
Provenance-based Data Trustworthiness Assessment in Data Streams
Hyo-Sang Lim - Purdue University
Dissecting Digital Data: Context & Meaning through Analytics
Marcus Rogers - Purdue University
Fast-flux Attacks
Shijie Zhou - University of Electronic Science and Technology of China
Human Factors Approaches to Preserving Privacy
Kelly Caine - Indiana University
Safely Analyzing Sensitive Network Data
Gerome Miklau - University of Massachusetts, Amherst
Some Thoughts on the Pervasive Trust Foundation for the Future Internet Architecture. A position presentation.
Leszek Lilien - Western Michigan University
Multi-Policy Access Control for Healthcare using Policy Machine
Zahid Pervaiz - Purdue University
Security in Infrastructureless and Decentralized Communication Networks - Possibilities, Results, and Evaluation Challenges
Andre Koenig - Technical University Darmstadt

Information Security Management and IT Executives in a Top Management Team
Juhee Kwon - Purdue University
PlugNPlay Trust for Embedded Communication Systems
Raquel Hill - Indiana University
Starting Over After A Lost Decade, In Search of a Bold New Vision for Cyber Security
Richard Power - CyLab - Carnegie Mellon
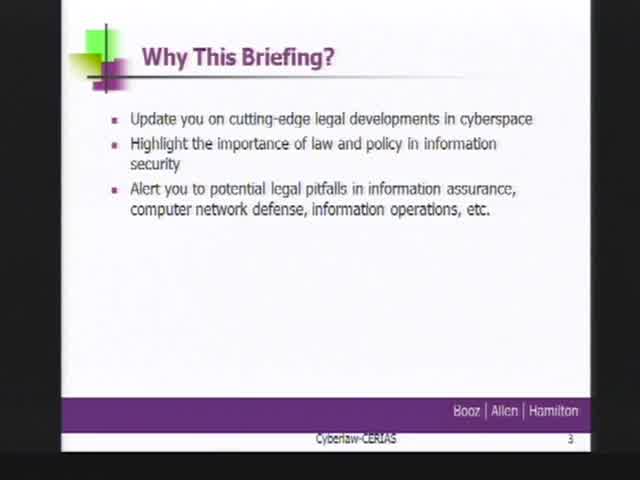
The Importance of Law in Cybersecurity, Recent Developments and Trends in Cyberlaw
Rick Aldrich - Booz Allen Hamilton
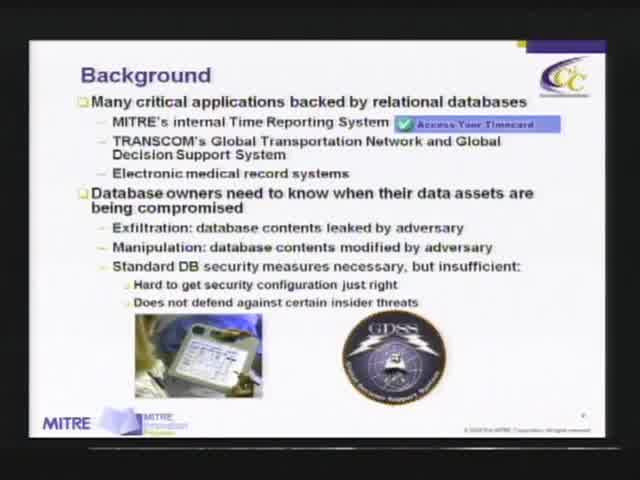
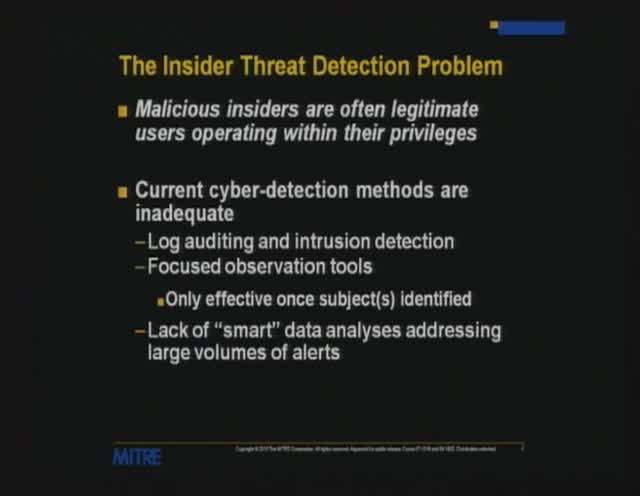
Database Assurance: Anomaly Detection for Relational Databases
Peter Mork - MITRE
Fake Picassos, Tampered History, and Digital Forgery: Protecting the Genealogy of Bits with Secure Provenance
Ragib Hasan - University of Illinois at Urbana-Champaign
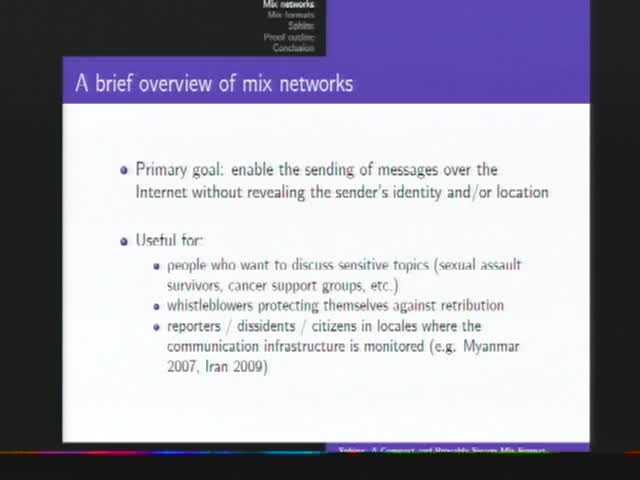
Sphinx: A Compact and Provably Secure Mix Format
Ian Goldberg - University of Waterloo
Privacy-Preserving Genome Computing Through Program Specialization
Xiaofeng Wang - Indiana University
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List