Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Showing: 476 to 500 of 940Affiliation shown is the affiliation at the time the talk was given.
User and Machine Authentication and Authorization Infrastructure for Distributed Testbeds
Torsten Braun - University of Bern
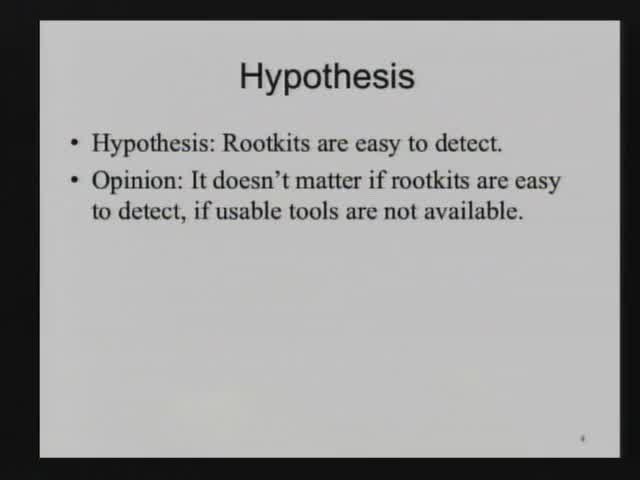
Kernel Malware Analysis with Un-tampered and Temporal Views of Dynamic Kernel Memory
Junghwan Rhee - Purdue University
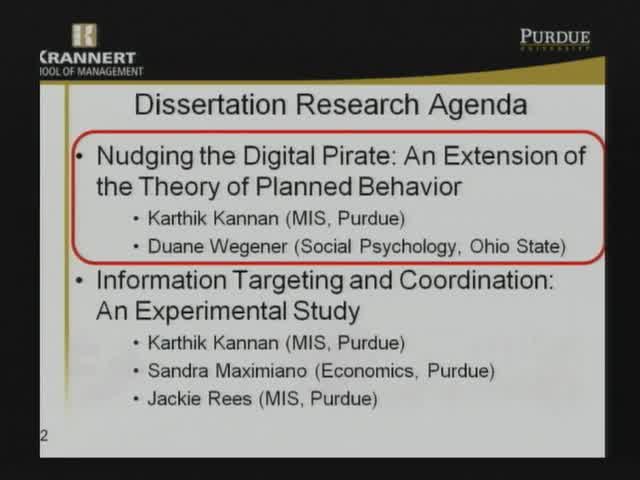
Nudging the Digital Pirate: Behavioral Issues in the Piracy Context
Matthew Hashim - Purdue University
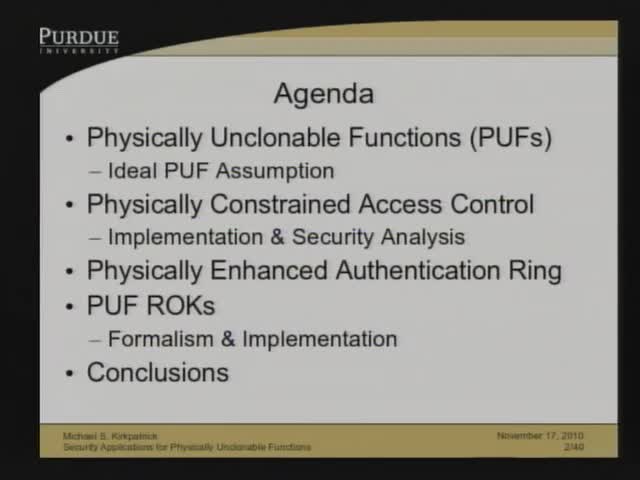
Security Applications for Physically Unclonable Functions
Michael Kirkpatrick - Purdue University
Detecting Coordinated Attacks with Traffic Analysis
Nikita Borisov - University of Illinois at Urbana-Champaign
The Role of Automata Theory in Software Verification
P. Madhusudan - University of Illinois at Urbana-Champaign
Trust and Protection in the Illinois Browser Operating System
Sam King - University of Illinois
Fast Regular Expression Matching using Small TCAMs for Network Intrusion Detection and Prevention Systems
Alex Liu - Michigan State University
Global Study of Web 2.0 Use in Organizations
Mihaela Vorvoreanu, Lorraine G. Kisselburgh - Purdue University
Assured Processing through Obfuscation
Sergey Panasyuk - Air Force Research Laboratory
Side Channel Threats in the Software-as-a-Service Era: Challenges and Responses
Xiaofeng Wang - Indiana University

Data in the Cloud: Authentication Without Leaking
Ashish Kundu - Purdue University
Secure Network Coding for Wireless Mesh Networks
Cristina Nita-Rotaru - Purdue University
Ontological Semantic Technology for Detecting Insider Threat and Social Engineering
Victor Raskin & Julia Taylor - Purdue University
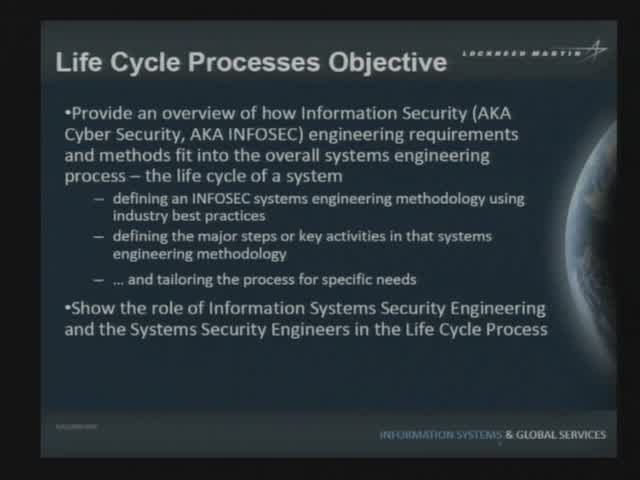
The role of System Security Engineering in the engineering lifecycle
Stephen Dill - Lockheed Martin
Security of JavaScript in a Browser Environment
Christian Hammer - Purdue University
60 years of scientific research in cryptography: a reflection
Yvo Desmedt - University College London, UK
Everything I Needed to Know about Security, I Learned in 1974
David Bell - Retired
A Platform for Creating Efficient, Robust, and Resilient Peer-to-Peer Systems
David Zage - Purdue University
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List