Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Affiliation shown is the affiliation at the time the talk was given.
Contactless Control Flow Monitoring via Electromagnetic Emanations
Sriharsha Etigowni - Purdue University
Identifying Security Risks Using Internet-Wide Scan Data
Morgan Princing - Censys
Immersive Virtual Insanity: Exploring Immersive Virtual Reality Security and Forensics
Abe Baggili - University of New Haven
Automated Reasoning of Security and Privacy of Cellular Networks
Syed Rafiul Hussain - Purdue University

Security, Ethics and the End of the World as We Know It
Doug Rapp - Delta Research & Cyber Leadership Alliance
Semantics-Driven, Learning-Based Privacy Discovery in Mobile Apps
Yuhong Nan - Purdue University
Physics-Based Approaches for creating Cyber Resilient Systems
Matt Mickelson - MITRE
Security and Privacy of Connected Autonomous Vehicles
Vireshwar Kumar - Purdue University
Everyone Wants to Help You: Understanding the Issues and Surviving with a Multitude of Regulatory Authorities
Leon Ravenna - KAR Global
Public Sector Cyber Security 2020: Challenges and Rewards
Bruce Coffing - City of Chicago

Proactive Endpoint and Network Security Operations. Detecting the Unknown Known
Corey Maypray - Eli Lilly
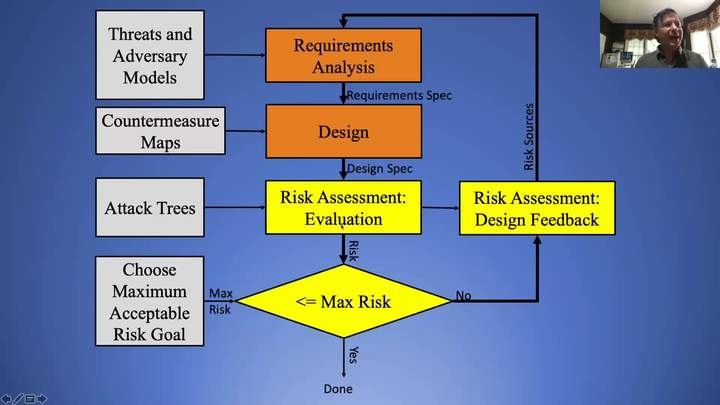
A Principled Approach to Cybersecurity Engineering
Sami Saydjari - Cyber Defense Agency, Inc.
Using Machine Learning for Network Intrusion Detection
Nandi Leslie - Raytheon
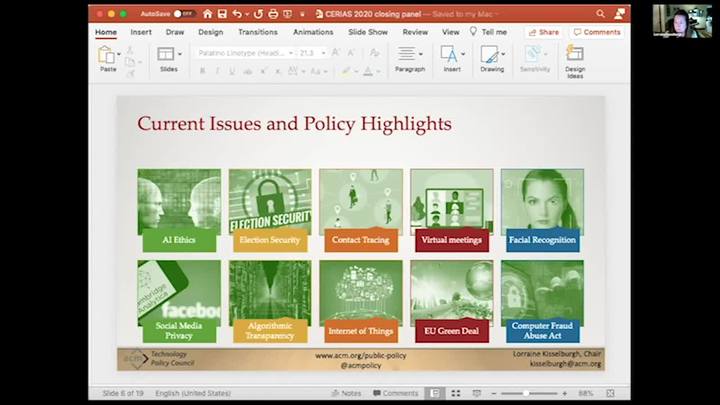
Election Security in the Age of COVID-19: Risk Management in the face of a "Perfect Storm"
Jim Richberg - Fortinet
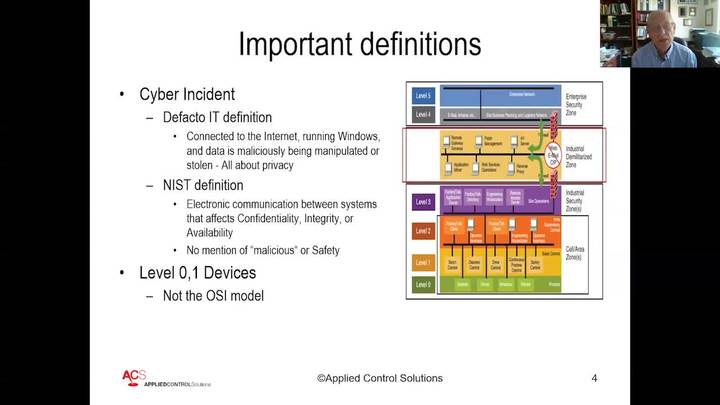
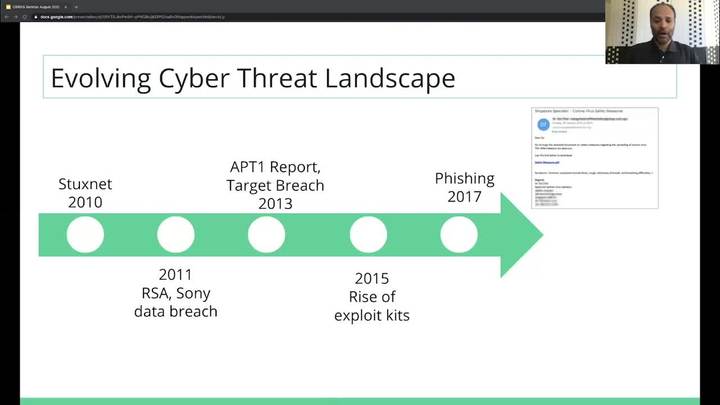
Cyber Security of Control Systems: The Second Coming of the Maginot Line
Joe Weiss - Applied Control Systems, LLC
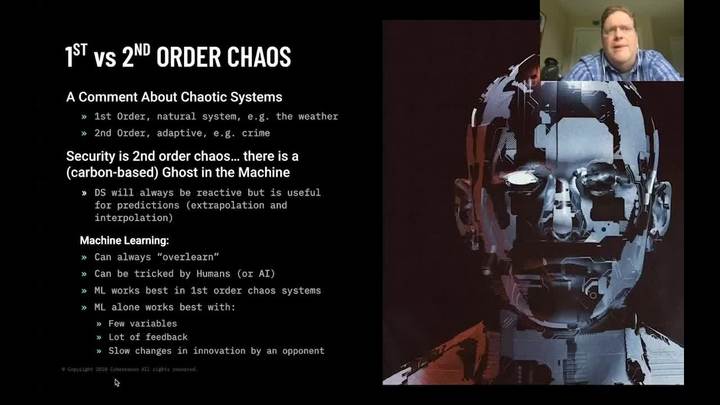
The Ghost in the Machine: Reconciling AI and Trust in the Connected World
Sam Curry and Alon Kaufman - Cybereason / Duality Technologies
Value of Cyber Threat Intelligence in Modern Security Operations
Shimon Modi - Elastic
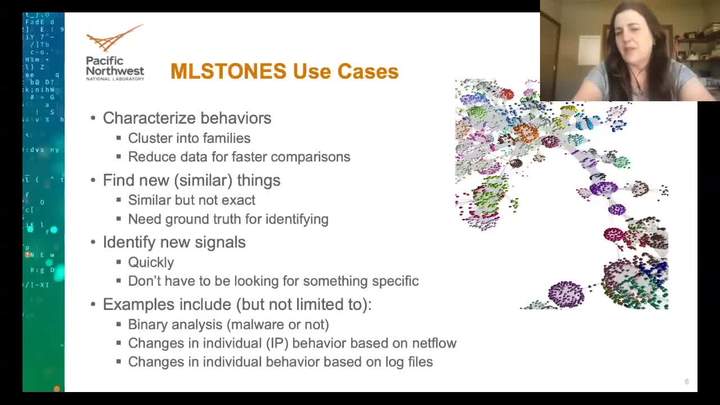
Flexible and Adaptive Malware Identification Using Techniques from Biology
Elena Peterson - Pacific Northwest National Laboratory

From Compliance in the Classroom to Compliance on the Street, Important Lessons That Every Cybersecurity Professional Must Know
Jeremiah Sahlberg - Tevora
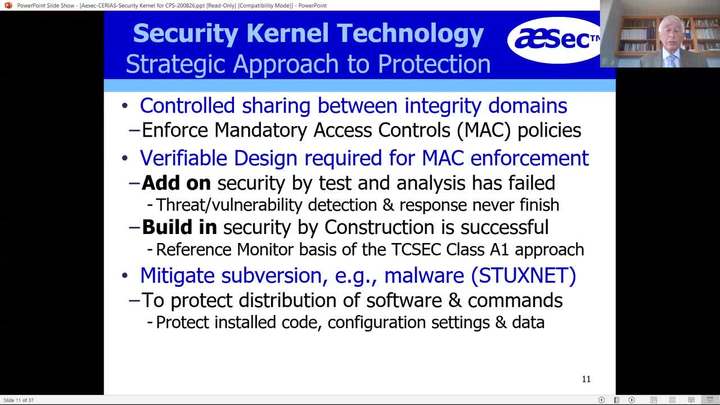
Dramatically Reducing Attack Surface Using Integrity MAC Security Kernel
Roger Schell - AESec Corporation
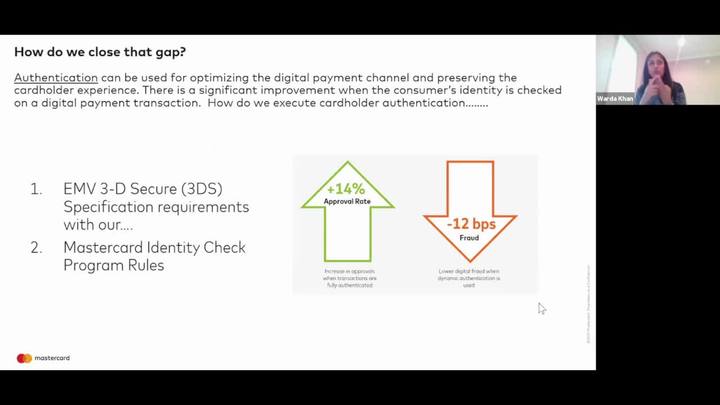
Authentication: Behind The Scenes When You Click "Check Out"
Warda Zahid Khan - Mastercard
From Machine Learning Threats to Machine Learning Protection Requirements
Michael Clark - Riverside Research
The Pod People Campaign: Driving User Traffic via Social Networks
Courtney Falk - GoDaddy
NUTS: eNcrypted Userdata Transit & Storage; Viewing Data as an Endpoint™ (DaaE) using Structured Cryptography
Yoon Auh - NUTS Technologies

Results from the Field: Cybersecurity in Nonprofits and Why it Matters
Kelley Misata - Sightline Security
Improving the Accuracy of Blocklists by Aggregation and Address Reuse Detection
Sivaram Ramanathan - University of Southern California
Maximizing Cyber Deception to Improve Security: An Empirical Analysis
Kimberly Ferguson-Walter - Laboratory for Advanced Cybersecurity Research, NSA Research

Security and Privacy for Humans
Lorrie Cranor - Carnegie Mellon University, CyLab
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List