Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Affiliation shown is the affiliation at the time the talk was given.
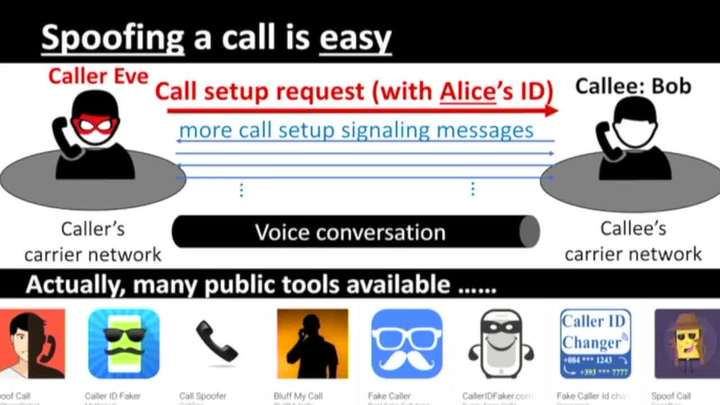
CEIVE: Combating Caller ID Spoofing on 4G Mobile Phones Via Callee-Only Inference & Verification
Haotian Deng - Purdue University

Secure Information Forwarding through Fragmentation in Delay- tolerant Networks
Sanjay Madria - Missouri University of Science and Technology
Trustable Information for Security Applications: Visual Analytics for Reliable, Effective Decision Making
David Ebert - Purdue University
Defending the Grid for Fun and Non-Profit: Cybersecurity and Infrastructure Resilience Research at LLNL
Steve Chapin - Lawrence Livermore National Laboratory
Protection against Compromised Operating Systems on ARM Cortex-A Architecture
Meng Yu - Roosevelt University

A Game Theoretic Approach for Adversarial Machine Learning -- When Big Data Meets Cyber Security
Bowei Xi - Purdue University

Game Theoretic Modeling of Cyber Deception in the Internet of Battlefield Things
Charles Kamhoua - US Army Research Laboratory

Securing IoT-based Cyber-Physical Human Systems against diverse attacks
Sathish Kumar - Coastal Carolina University
Efficient and Constant-Round Secure Comparison through Function Transformation, Dynamic Group Switching and Asymmetric Computation
Wei Jiang - University of Missouri-Columbia
Hardware Cybersecurity Attacks and Some Solutions
Krishna Kavi - University of North Texas

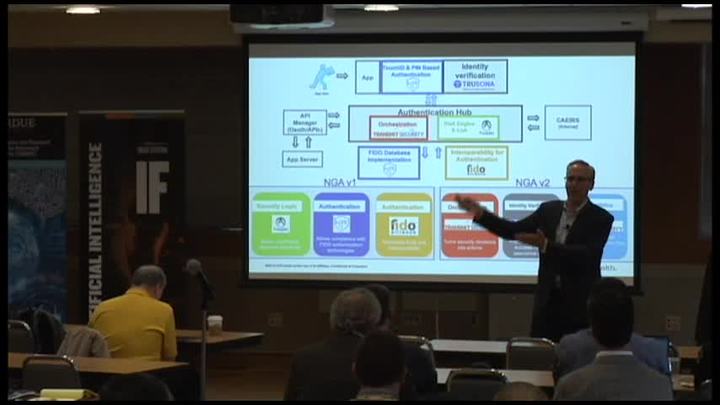
Protecting your online Identity in a world of modern application architecture
Robert Mundt - Eli Lilly and Company

The Purdue Live Security Analyzer (PULSAR)
Lauren Featherstun, Shivam Trivedi, Brian Werts, Erik Gough - Purdue University

A New Approach to Distributed Hypothesis Testing and Non-Bayesian Learning: Improved Learning Rate and Byzantine Resilience
Aritra Mitra - Purdue University
Moving Target Defense for a Serial Communication Protocol
Chris Jenkins - Sandia National Laboratories
Forensic Identification of Fake Digital Photographs
Chet Hosmer - Python Forensics, Inc.

'Networking' Skills for Cybersecurity
Andrew Rozema - Grand Rapids Community College

Bitcoin and other dreams of utopian thinking-what happens when they meet reality?
Mitch Parker - IU Health
Hacking Stressed: Frustration, burnout, and the pursuit of happiness
Celeste Paul - National Security Agency
Forgetting the Forgotten: Conceal Content Deletions from Persistent Observers
Mohsen Minaei - Purdue University
Fingerprinting Encrypted Voice Commands on Smart Speakers
Boyang Wang - University of Cincinnati
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List