Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Showing: 351 to 375 of 940Affiliation shown is the affiliation at the time the talk was given.
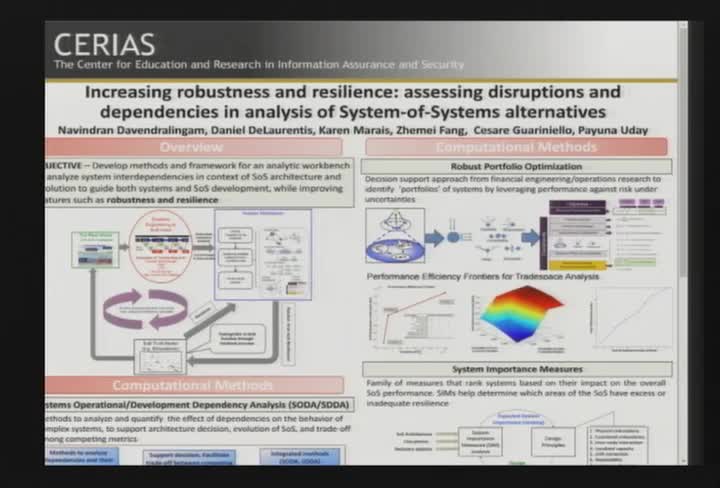
CERIAS Poster Contest Winners
Rohit Ranchal & Payuna Uday & Zhemei Fang - Purdue University
Engineering Secure Computation -- Efficiently
Yan Huang - Indiana University
Privacy Potpourri: Changing Privacy from the Bottom Up
Rebecca Herold - Rebecca Herold & Associates, LLC
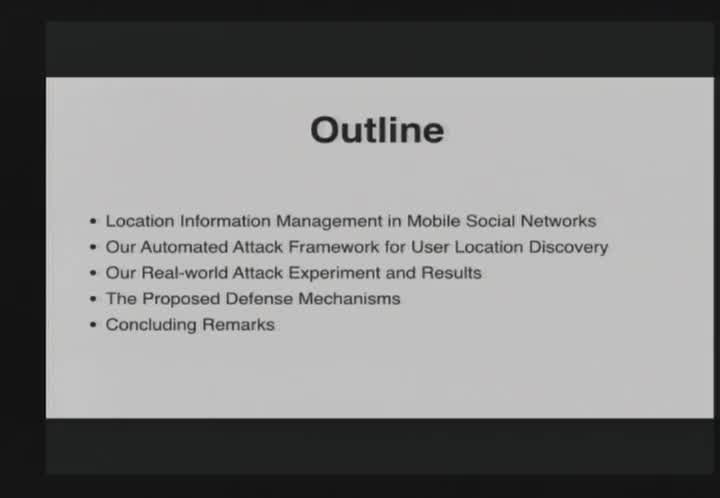
Breaking Mobile Social Networks for Automated User Location Tracking
Kui Ren - University at Buffalo
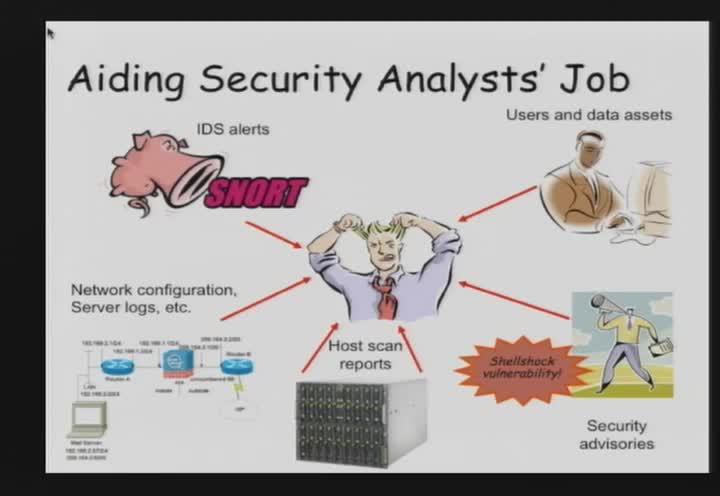
Aiding Security Analytics -- From Dempster-Shafer Theory to Anthropology
Xinming Ou - Kansas State University
Software updates: decisions and security implications
Kami Vaniea - Indiana University
Privacy Notions for Data Publishing and Analysis
Ninghui Li - Purdue University

Regulatory Compliance Checking Over Encrypted Audit Logs
Omar Chowdhury - Purdue University
Practical Confidentiality Preserving Big Data Analysis in Untrusted Clouds
Savvas Savvides - Purdue University
Security with Privacy - A Research Agenda
Bharath Samanthula - Purdue University

Learning from Information Security Maturity: A Textual Analysis
Jackie Rees Ulmer - Purdue University
How Program Analysis can be Used in Security Applications
Xiangyu Zhang - Purdue University
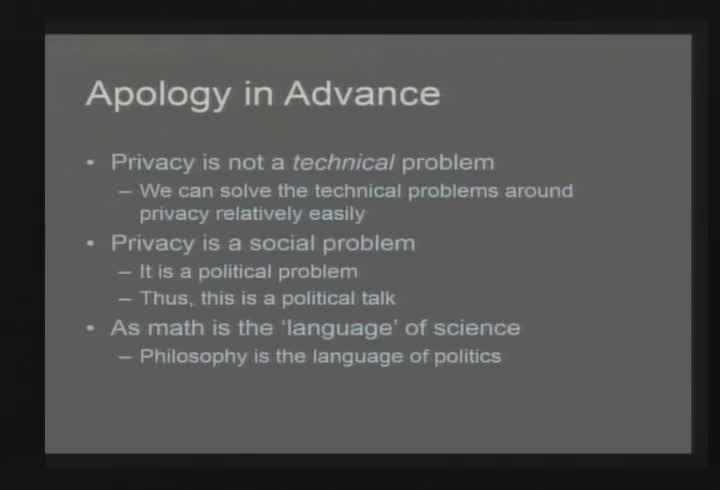
Privacy in the Age of the Police State
Marcus Ranum - Tenable Network Security

You can hack, but you can't hide: Using log analysis to detect APTs
Kevin Bowers - RSA
Improving Analyst Team Performance and Capability in NOC / SOC Operations Centers
Barrett Caldwell and Omar Eldardiry - Purdue University
Healthcare Security and Privacy: Not There Yet
Robert Zimmerman - Inforistec

"Memory Analysis, Meet GPU Malware"
Golden G. Richard III - University of New Orleans
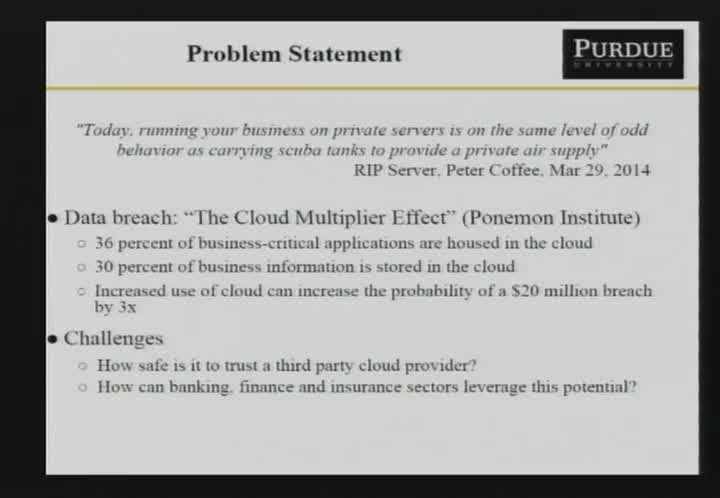
Responsible Information Management and the 2014 Cost of Data Breach: Global Analysis
Larry Ponemon - Ponemon Institute
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List