Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Affiliation shown is the affiliation at the time the talk was given.

Net Trust: Identification Through Social Context
Jean Camp - Indiana University
Digital Identity Management and Theft Protection
Abhilasha Bhargav-Spantzel - Purdue University
Categories of Digital Forensic Investigation Techniques
Brian Carrier - Purdue University
Hamsa: Fast Signature Generation for Zero-day Polymorphic Worms with Provable Attack Resilience
Yan Chen - Northwestern University
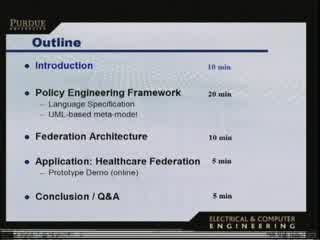
A Policy Engineering Framework for Federated Access Management
Rafae Bhatti - Purdue University
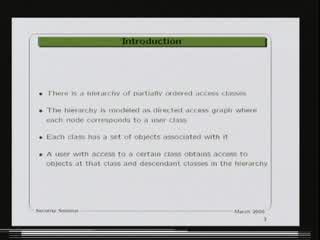
Dynamic and Efficient Key Management for Access Hierarchies
Marina Blanton - Purdue University
Privacy Policies in Web-based Healthcare
Julie Earp - North Carolina State University

Spoofing-resistant Packet Routing for the Internet"
Minaxi Gupta - Indiana University

Chaos,Complexity, Cybernetics and Therminator:
Dave Ford - Naval Postgraduate School
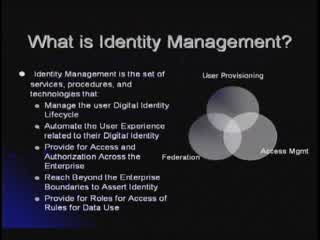
Identity Management Strategies and Integration Perspectives
David Carroll - MITRE
On the Evolution of Adversary Models for Security Protocols - from the Beginning to Sensor Networks
Virgil D. Gligor - University of Maryland
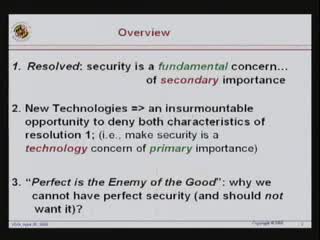
Toward Autonomic Security Policy Management
Ehab Al-Shaer, Ph.D. - DePaul University, Chicago, IL

Invasive Browser Sniffing and Countermeasures
Sid Stamm - Indiana University
A Multi-layered Approach to Web Application Defense
Ed Finkler - Purdue University
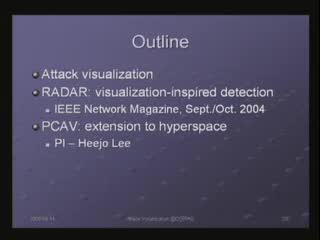
Real-Time Visualization of Network Attacks on High-Speed Links
Hyogon Kim - Korea University/PU Visitor
Prioritizing Processes and Controls for Effective and Measurable Security
Gene Kim - Tripwire, Inc
The Secure Information Sharing Problem and Solution Approaches
Ravi Sandhu - George Mason University
Verification of Integrity for Outsourced Content Publishing and Database Queries
Danfeng Yao - Brown University
Network Security Begins at Home: Changing Consumer Behavior for i-Safety
Nora Rifon - Michigan State University
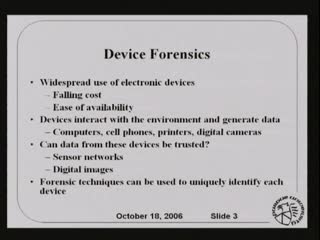
Forensics Characterization of Printers and Image Capture devices
Nitin Khanna
Beyond Separation of Duty: An Algebra for Specifying High-level Security Policies
Qihua Wang - Purdue University
Developing an Operational Framework for Integrated System Security
Paula DeWitte - St. Mary’s Law School in San Antonio
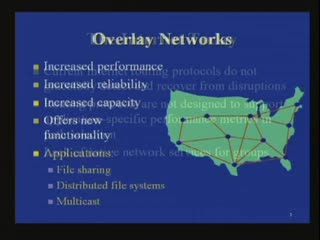
Mitigating Attacks Against Measurement-Based Adaptation Mechanisms in Unstructured Multicast Overlay Networks
David Zage - Purdue University

One Step Forward, Two Steps Back, or Two Steps Forward, One Step Back: A Ten Year Retrospective on Cyber Crime and Cyber Security (1996-2006)
Richard Power - GS(3) Intelligence & Words of Power

OS-Level Taint Analysis for Malware Investigation and Defense
Dongyan Xu - Purdue University
The Psychology of Computer Deviance: How it can assist in digital evidence analysis.
Marc Rogers - Purdue University
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List