Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Affiliation shown is the affiliation at the time the talk was given.
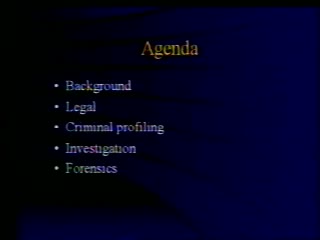
PFIRES: Policy Framework for Interpreting Risk in eCommerce Security
Jackie Rees - Krannert School of Management at Purdue University
NLP for IAS: Overview and Implementations
Victor Raskin - English and Linguistics at Purdue University
Commercial High-Resolution Satellite Imagery Polic
Gerald Thomas - Political Science, Purdue University
Tracing Denial-of-Service Attacks; or why we may never know who attacked Yahoo et. al.
Clay Shields - CERIAS, Purdue University
Automatic identification of classified documents
Judy Hochberg - Computer Research and Applications Group (CIC-3) at Los Alamos National Laboratory
Algorithms for Internet Security Services
Michael T. Goodrich - Johns Hopkins University
Implications of Mobile Code on Microsoft Platforms
Padgett Peterson - Lockheed Martin
Machine Learning Techniques for Anomaly Detection in Computer Security
Terran Lane - Purdue University
Information Assurance: The Army's Perspective
Phil Loranger - United States Army

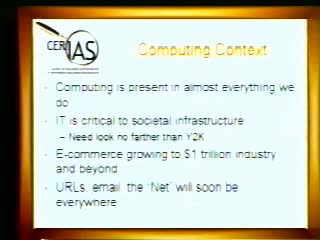
Information Assurance Challenges for the 21st Century
Michael G. Fleming & Victor Maconachy - NSA

The Holy Grail of E-Business Risk Management: Creating and Sustaining the Insurable Standard for E-Business Security and Assurance
Rick Davis - Aon Corporation
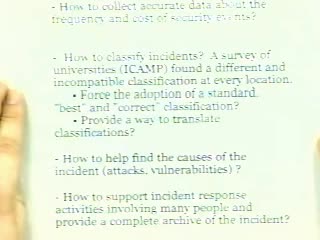
The IRDB Project: An Incident Response Database For Gathering Cost And Incidence Information On Types of Security Events
Pascal Meunier - CERIAS
Everything I Needed to Know about Network Security I Learned at the Tower of London
William Hugh Murray - CISSP
Richard Stotts, Jerome Webb & Matthew Beebe
Richard Stotts, Jerome Webb & Matthew Beebe - United States Air Force
Developing Data Mining Techniques for Intrusion Detection: A Progress Report
Wenke Lee - North Carolina State University
Fault Tolerant Authentication in Mobile Computing
Bharat Bhargava - Purdue University
Fast Encryption and Authentication in One Shot
Virgil Gligor - University of Maryland
A Security Architecture for Survivable Systems
Chenxi Wang - University of Virginia
Our Policy is to Violate Your Privacy: When Privacy Goals Conflict
Annie Anton - North Carolina State University
Detecting Computer Attackers: Recognizing Patterns of Malicious, Stealthy Behavior
Robert Cunningham - MIT Lincoln Laboratory, Information Systems Technology
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List