Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Showing: 151 to 175 of 940Affiliation shown is the affiliation at the time the talk was given.
AI, Computational Imaging and the Battle for Media Integrity
Nasir Memon - NYU Tandon

A Formal Verifier for the Diem Blockchain Move Language
David Dill - Facebook

Educating the Next Generation on the Challenges of Securing Critical Infrastructure
Dave Henthorn - Rose-Hulman
Big Breaches: Cybersecurity Lessons For Everyone
Neil Daswani - Daswani Enterprises

National Security Implications of Quantum Technology
Laura Thomas - ColdQuanta
Security Engineering for Machine Learning
Gary McGraw - Berryville Institute of Machine Learning

Cybersecurity Skills – Easy to say, harder to recognise?
Steven Furnell - University of Nottingham in the United Kingdom

Delving into differential privacy and anomaly detection: a meta-learning perspective
Yimin Chen - Virginia Tech

The Invisible Risks: An Empirical Analysis on Data Sharing Activities and Systemic Risk among the Data Brokers
Tawei (David) Wang - DePaul University
Practical software Supply Chain Security and Transparency
Santiago Torres-Arias - Purdue University

SDN/NFV in the ICS, SCADA and Manufacturing World as a Cyber Security Tool
Greg Akers - Executive Technology Consultant
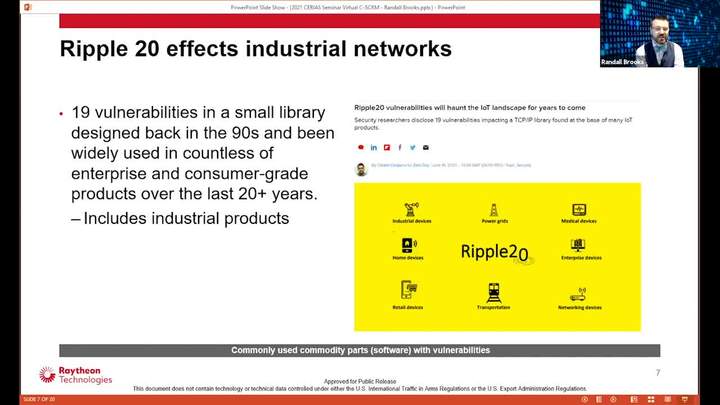
Cyber Supply Chain Risk Management (SCRM) and its impact on information and Operational Technology (IT/OT)
Randall Brooks - Raytheon

Technology, Self-Determination, and the Future of the Future
Cory Doctorow - Electronic Frontier Foundation
Securing the Software Supply Chain
Levi Lloyd - Lawrence Livermore National Laboratory
Lessons Learned – Fifty Years of Mistakes in Cybersecurity
Steve Lipner - SAFECode
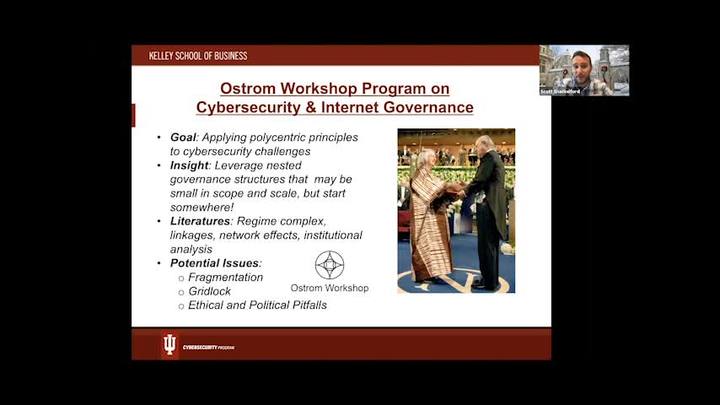
The Internet of Things: What Everyone Needs to Know
Scott Shackelford - Indiana University
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List