Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Showing: 101 to 125 of 940Affiliation shown is the affiliation at the time the talk was given.

Chinese Views of Information and Future Warfare
Dean Cheng - Potomac Institute for Policy Studies

Problems and Challenges in Data Security Posture Management
Mummoorthy Murugesan - Normalyze, Inc.
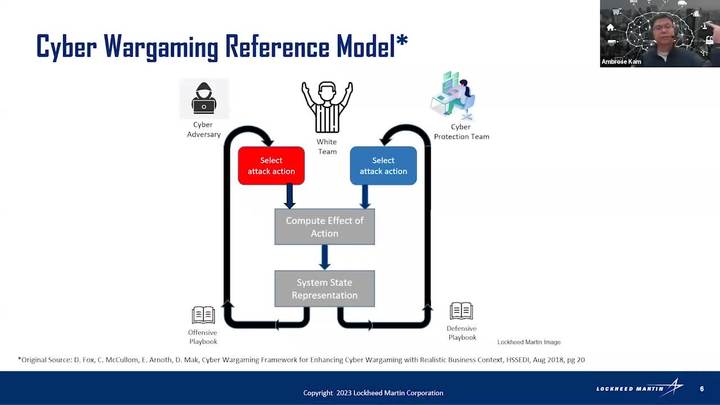
Applying Multi-Agent Reinforcement Learning (MARL) in a Cyber Wargame Engine
Ambrose Kam - Lockheed Martin
Users Are Not Stupid: Six Cybersecurity Pitfalls Overturned
Julie Haney - National Institute of Standards and Technologies

Fast and Reliable Formal Verification of Smart Contracts with the Move Prover
Meng Xu - University of Waterloo

Making Cybersecurity Reliable and Cybersecurity Careers Rewarding
Brian Barnier & Prachee Kale - Think.Design.Cyber

Data, Privacy---and the Interactions Between Them
Christine Task - Knexus Research Corporation
Program Maturity - Cybersecurity and Operational Risk Management
Gideon Rasmussen
Security and Privacy in the Cyber-physical World
Ning Zhang - Washington University in St. Louis
Stop Selling Cybersecurity Short!: Cybersecurity as a Component of National Power
David C. Benson - United States Air Force

Ransomware and the Future of Cyberwarfare
Maggie MacAlpine - MITRE Engenuity
Adaptive Multi-Factor Authentication & Cyber Identity
Dipankar Dasgupta - The University of Memphis
"With great power comes great responsibility" – Responsible Cybersecurity Innovations and Investments for Cloud Computing
Abhilasha Bhargav-Spantzel & Sonnie Ebikwo - Microsoft
IoT Device Security in a Zero Trust Environment
Kevin Kornegay - Morgan State University

Securing Connected Devices – Challenge and Opportunities
Máire O'Neill - Queen's University Belfast
Enabling a Practically Secure Mobile Networked System
Dr. Guan-Hua (Scott) Tu - Michigan State University

Crowd Forecasting to Enhance Cybersecurity
Paul Rosenzweig - Red Branch Consulting

Automated Function Boundary Detection in Stripped Binaries
Jim Alves-Foss - University of Idaho
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List