Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Showing: 51 to 75 of 940Affiliation shown is the affiliation at the time the talk was given.

Behavioral Advertising and Consumer Welfare
Alessandro Acquisti - Carnegie Mellon
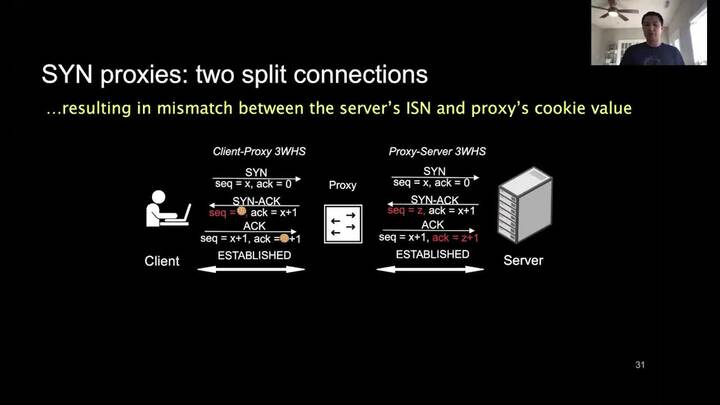
SmartCookie: Blocking Large-Scale SYN Floods with a Split-Proxy Defense on Programmable Data Planes
Xiaoqi Chen

The Road Towards Accurate, Scalable and Robust Graph-based Security Analytics: Where Are We Now?
Zhou Li - University of California, Irvine
Dissecting the Software Supply Chain of Modern Industrial Control Systems
Michail Maniatakos - NYU Abu Dhabi
Shamrock Cyber – When Luck Just Isn't Enough
Chance Younkin - Pacific Northwest National Laboratory
Exploiting Vulnerabilities in AI-Enabled UAV: Attacks and Defense Mechanisms
Ashok Vardhan Raja - Purdue University Northwest

IDART (Information Design Assurance Red Team): A Red Team Assessment Methodology
Russel Waymire - Sandia

Empowering the Next Generation of Digital Defenders: Ethics in Cybersecurity and Emerging Technologies
Chris Kubecka de Medina - HypaSec
AI's Security Maze: Navigating AI's Top Cybersecurity Risks Through Strategic Planning and Resilient Operations
David Haddad - Purdue University

Privacy and Security in ML: A Priority, not an Afterthought
Shagufta Mehnaz - The Pennsylvania State University
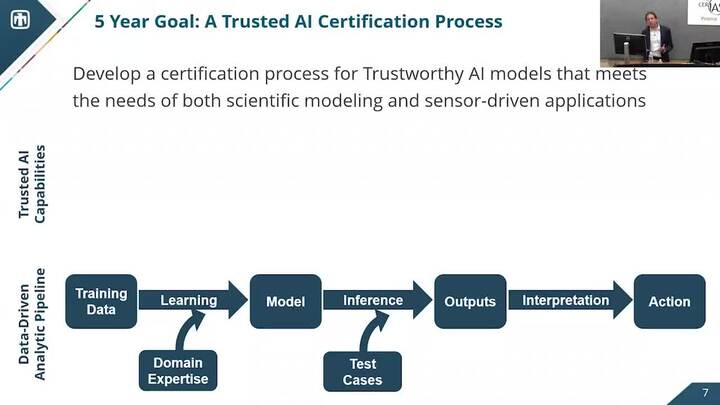
Defining Trusted Artificial Intelligence for the National Security Space
David Stracuzzi - Sandia National Laboratories
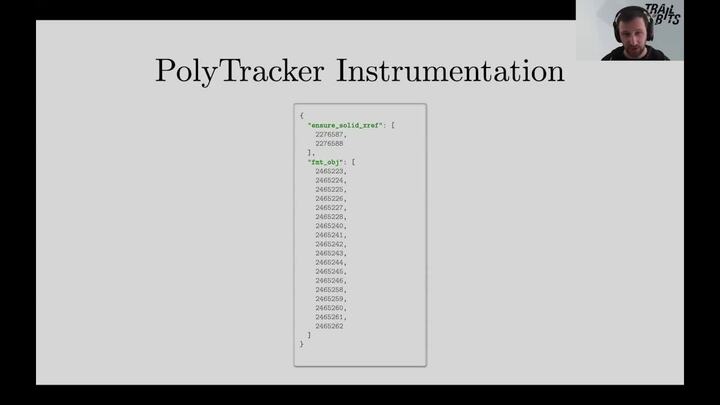
In Pursuit of Silent Flaws: Dataflow Analysis for Bugfinding and Triage
Evan Sultanik - Trail of Bits
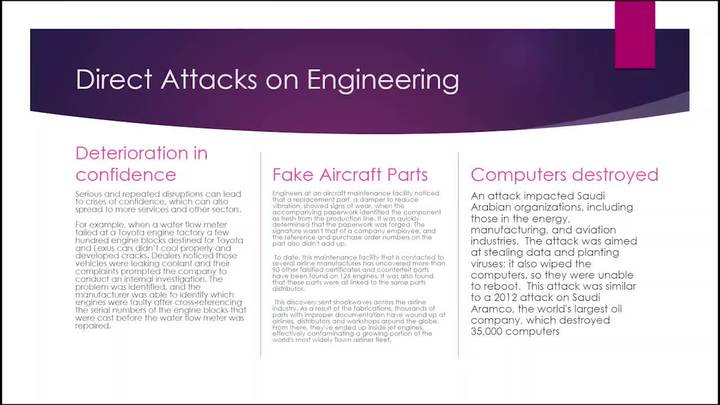
Secure Sourcing of COTS Products: A Critical Missing Element in Software Engineering Education
Daniel Shoemaker - University of Detroit Mercy
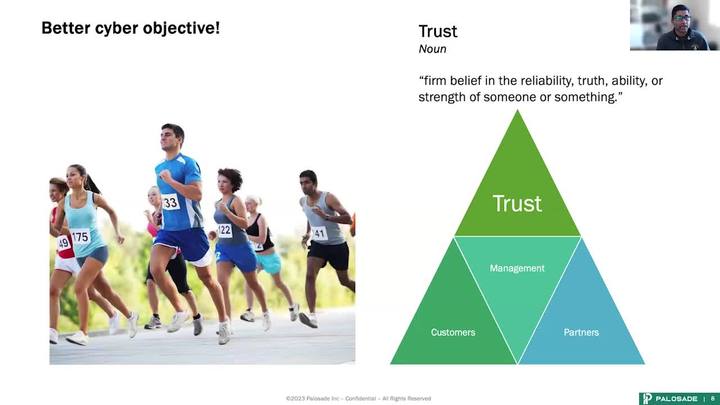
The Importance of Security by Design & The Importance of Including Cybersecurity Experts in Your Business Decisions
Douglas Huelsbeck - DoD
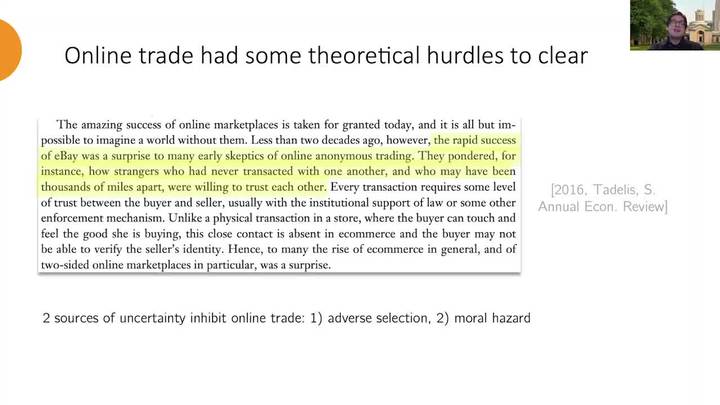
The Fault in Our Stars: How Reputation Systems Fail in Practice
Alejandro Cuevas - Carnegie Mellon University
Stepping Through Cybersecurity Risk Management A Systems Thinking Approach
Jennifer Bayuk - Jennifer L. Bayuk, LLC

On Security Operations for AI Systems
Jonathan (Jono) Spring - Cybersecurity and Infrastructure Security Agency (CISA)
Tensor Decomposition Methods for Cybersecurity
Maksim Eren - Los Alamos National Laboratory

Multifactor Authentication - The Problem, Recommendations, and Future Concerns
William Malik - Malik Consulting

Enhancing Cybersecurity via Lessons Learned from the Evolution of Malware
Solomon Sonya - Purdue University

Invisible Signatures: Device Fingerprinting in a Connected World
Sandhya Aneja - Marist College
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List