Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Showing: 651 to 675 of 940Affiliation shown is the affiliation at the time the talk was given.
Where's the FEEB? Effectiveness of Instruction Set Randomization
David Evans - University of Virginia
Using process labels to obtain forensic and traceback information
Florian Buchholz - Purdue University
Perturbation of Multivariable Public-key Cryptosystems
Jintai Ding - University of Cincinnati
Network Data Streaming - A Computer Scientist's Journey in Signal Processing
Jun Xu - Georgia Tech
Obfuscated Databases: Definitions and Constructions
Vitaly Shmatikov - University of Texas at Austin
Self Healing Cyber Databases Under Malicious Attacks
Peng Liu - Pennsylvania State
Hidden Access Control Policies with Hidden Credentials
Keith Frikken - Purdue University
Survivable routing in wireless ad hoc networks
Cristina Nita-Rotaru - Purdue University

Using Statistical Analysis to Locate Spam Web Pages
Dennis Fetterly - Microsoft
Attribute-Based Access Control
William Winsborough - George Mason University
An Anonymous Fair-Exchange E-Commerce Protocol
Indrakshi Ray - Colorado State University
GTRBAC: A Generalized Temporal Role Based Access Control Model
James Joshi - Pittsburgh University
Towards Mining Syslog Data
Abe Singer - University of California at San Diego
Robustness testing - black-box testing for software security
Ari Takanen - Codenomicon Ltd.
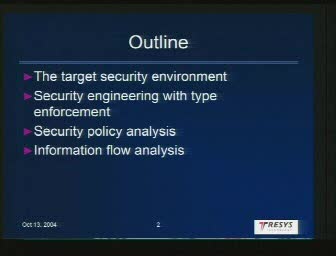
Information Flow Analysis in Security Enhanced Linux
Dan Thomsen - Tresys Technology
How to Forge Signatures and Be Happy About It
Giuseppe Ateniese - Johns Hopkins University
Automatic Generation and Analysis of Attack Graphs
Jeannette Wing - Carnegie Mellon University
Samuel D. Conte Distinguished Lecture Series
John Mitchell - Stanford University
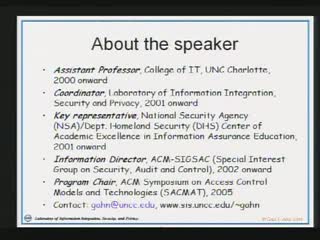
Secure Information Sharing within a Collaborative Environment
Gail-Joon Ahn - University of North Carolina at Charlotte
Administrative Scope and Role-Based Administration
Jason Crampton - Royal Holloway, University of London

Application of Thermodynamics to Computer Network Defense
Dave Ford - Naval Postgraduate School
Retrofitting Security to Internet Infrastructure Protocols
Russ Mundy - Sparta
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List