Archive
2026 | 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 | 2014 | 2013 | 2012 | 2011 | 2010 | 2009 | 2008 | 2007 | 2006 | 2005 | 2004 | 2003 | 2002 | 2001 | 2000 | 1999 | 1998 | 1997 | 1996 | 1995 | 1994 |
Results
Showing: 626 to 650 of 940Affiliation shown is the affiliation at the time the talk was given.
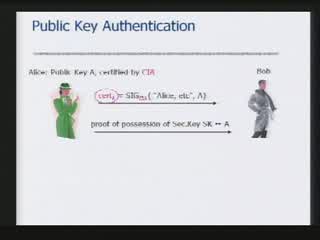
Digital Identity Management and Theft Protection
Abhilasha Bhargav-Spantzel - Purdue University

Net Trust: Identification Through Social Context
Jean Camp - Indiana University
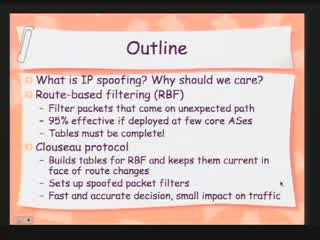
Clouseau: A practical IP spoofing defense through route-based filtering
Jelena Mirkovic - University of Delaware
Privacy-preserving Policy-driven Access Control with Mixed Credentials
Shouhuai Xu - University of Texas at San Antonio
Privacy and anonymity in Trust Negotiations".
Anna Squicciarini - University of Milano
The Ontology of Documents and the Technology of Identification
Barry Smith - SUNY Buffalo
A Demonstration in the Need for a Layered Security Model
Bryant G. Tow - Unisys
Aligning Privacy Values, Policies, Law and Software Requirements
Annie Anton - North Carolina State University/ Associate Professor and Director, ThePrivacyPlace.Org
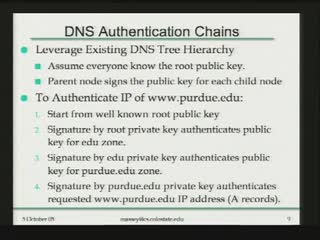
Securing the Internet's Domain Name System
Dan Massey - Colorado State University
Managing Risk of Information Systems Security Incidents
Dr. Fariborz Farahmand - Purdue University/CERIAS
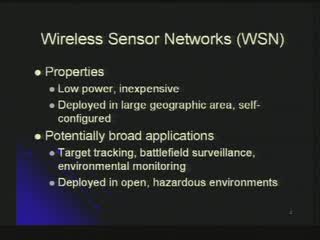
A Framework for Identifying Compromised Nodes in Sensor Networks
Ting Yu - North Carolina State University
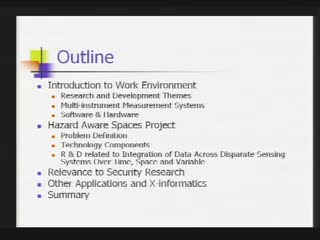
Toward Hazard Aware Spaces: Knowing Where, When and What Hazards Occur
Peter Bajcsy - University of Illinois at Urbana-Champaign/ National Center for Supercomputing Applications (NCSA)
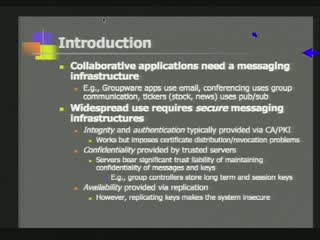
Minimizing Trust Liabilities in Secure Group Messaging Infrastructures
Himanshu Khurana - University of Illinois at Urbana-Champaign

An Introduction to Biometric Technologies
Stephen Elliott - Purdue University
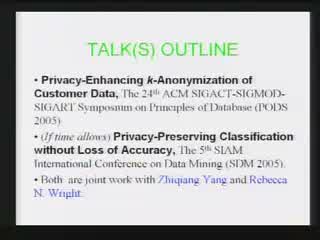
PrivacyEnhancing k-Anonymization of Customer Data
Sheng Zhong - SUNY at Buffalo

Traust and PeerTrust2: Applying Trust Negotiation to Real Systems
Marianne Winslett - University of Illinois at Urbana-Champaign
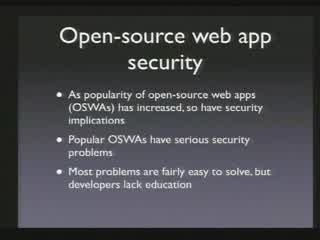
Vulnerability-Driven Network Filters for Preventing Known Vulnerability Attacks
Helen J. Wang - Microsoft Research
Ways to Watch

Watch Now!
Over 500 videos of our weekly seminar and symposia keynotes are available on our YouTube Channel. Also check out Spaf's YouTube Channel. Subscribe today!- Upcoming
- Past Seminars
- Previous Speakers
- Open Dates (Fall/Spring)
- Attending the Seminar
- About the Weekly Seminar
- CPE Credit Information (PDF)
- Join our Mailing List