The Center for Education and Research in Information Assurance and Security (CERIAS)
The Center for Education and Research inInformation Assurance and Security (CERIAS)
Not allowed to work from home so I don't
My job recently told me that even during the snowstorm we got earlier this week, I am not allowed to work from home at all. Even though I work in IT and do everything remotely, they want me in the office.
So I deleted Teams and my email off my phone. I am no longer available after hours.
My boss tried to call me for something urgent last night and couldn't reach me. He asked why today and I explained to him what I was told.
I am not allowed to work from home.
It prompted me to think of several instances where I have engaged in behavior that might be described as malicious compliance; I prefer to think of them as instances of "security compliance education." Here's one such instance that my students see enjoy hearing about.
In 2000, we got some funding from a US federal agency (which will be unnamed) to explore for potential vulnerabilities in a commercial printer/copier combination. My technical point of contact (POC) told me that we didn't need to file any reports until we had some results. Apparently, he didn't convey this to the agency business person because the contract specified a long, convoluted monthly report. I was forcibly reminded of this requirement a week after the contract was finalized, even though it was in the midst of the winter break, and absolutely nothing had happened -- or would happen, for at least another month.
I grumbled a bit but compiled the report with basically "nothing to report" and "nothing spent" in the various sections and uploaded it via FTP to their designated site as a PDF.
Now, it is important to this story that my standard computers for use at the time were Sun workstations and Macintosh systems. Most of the research we did was on these systems, and our papers and reports were produced using LaTeX. We avoided Windows because it was usually so buggy (blue screens) and so prone to security problems. We also avoided Word because (a) it was (and is) annoying, and (b) it was a common vector for computer viruses. Thus, my monthly report was produced using LaTeX.
Two weeks into the semester, I got an email from some clerk at the sponsoring agency noting that the monthly report must be submitted as a Word document; the contract specified Word and only Word, and I must submit the report as a Word document, with no deviation allowed. I placed a call to my POC, and he indicated, apologetically, that he could not alter the terms as they were standard for the agency involved: everyone had to abide by them.
Grrrrr....
So, after a little thought,1 I produced the next monthly report in LaTeX as before. I produced a PDF of the report and printed it. Then, I scanned each sheet individually into a graphic file (.pic, as I recall). I then rebooted one of our Windows machines2 into MS-DOS and loaded up the oldest version of MS Word I could locate. After consulting the manual, I created a document where each page contained an image -- the corresponding image for that page of the report I had prepared. I saved it out to disk (it was huge), and uploaded it to the sponsor FTP site. Yes, it was basically a huge file of graphic images, but it was technically a Word file.
The next day I got an automated response noting the submission. Three days later, I got an email asking if the report was what I actually intended to upload. I responded that yes, it was. I indicated it had all the required information and was most definitely a Word document. I also alerted my POC about the upload (he was amused).
Another few days later and I got email from the original person who had complained about the PDF now complaining they were having difficulty with the file. I responded that the contract required Word, and that is what I used -- I wasn't responsible for their IT issues.
In month 3, I went through the same procedure but didn't have the email exchanges. Purdue then got an email from the agency business office stating that they were altering their standard business practices to allow all contractor reports to be submitted in Word -or- PDF. Would we mind submitting PDF henceforth? I briefly weighed the idea of continuing my production of Word versions of the report but decided that changing the business practices of a whole federal agency was enough.
Footnotes:
1. Someone once asked me why I didn't send them a Word document with some mischevious macros. I replied "USC 18 § 1030" (that's the Computer Fraud and Abuse Act).
2. Microsoft was a CERIAS partner at the time. When their rep visited, he saw that the lab was equipped with only Sun machines and Macintoshes. A few weeks later, we had several nice servers with Windows preinstalled delivered to the CERIAS lab. All our existing systems were named after mythical and fictional places (e.g., Amber, Oz, Dorsai, Uqbar), and we wanted to continue that scheme. We collectively decided to name the new machines Hel, Tartarus, and Niflheim. When he next visited and saw the machines, with nametags attached, he smiled a little. Two weeks later, we got another three, and they got related names; I can't recall exactly, but I think they were Underworld, Mictlan, and Jahannam). At his next visit, he remarked he could send us a lot more machines. I said we'd find a home for them, and welcome the chance to engage more of our philosophy, history, and literature faculty in the process.
All that said, we actually had a great working relationship with MS, and they hired a lot of our graduates. The machines did get a lot of use in experiments and classes.
If you haven't reached your quota yet for hearing from Santa Spaf, here are three recent podcasts where I was interviewed on a variety of topics. One common theme: The role of people in cybersecurity. A second theme: Some future trends.
In the 100th episode of CISO Stories: Discussion with Gene Spafford on some of the common cybersecurity myths and how to better cope with the changing environment. Join here.
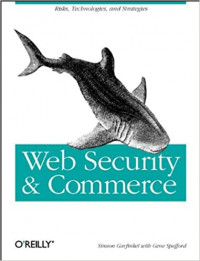
For those of you interested in more info on the book discussed in the podcast, see this InformIT site. If you preorder now, you can get a 35% discount with code CYBERMM.
A longer info sheet is available here.
Cybersecurity and privacy have several notable professional associations associated with them. Some, such as ACM, the IEEE Computer Society, and IFIP are more generally about computing. One of the societies specifically directed to cybersecurity is the ISSA -- the Information Systems Security Association International. ISSA promotes the development and standards of the profession, globally.
Each year, ISSA recognizes individuals who have made significant contributions to the association and to the field overall. In prior years, both Professor Elisa Bertino and Professor Eugene Spafford have been recognized by ISSA: both have been inducted into the ISSA Hall of Fame, and Spaf has been named as a Distinguished Fellow of the organization.
ISSA has announced its 2022 honorees. Our congratulations to all these people for their accomplishments and this recognition!
Of particular note, three of the honorees have spoken in CERIAS seminars and events:
We also note the ISSA Education Foundation, which supports scholarships for students in the field. Two of those scholarships are in memory of individuals who were long-time friends of CERIAS, Howard Schmidt and Gene Schultz. The recent give-away of Spaf's coffee mugs raised over $1000 for those scholarships. We encourage others to consider contributing to the foundation to support worthy students. Also, the ISSAEF is an Amazon Smile participant, so that is a painless way for you to make ongoing donations (see the ISSAEF page for a link).
Want to get some authentic CERIAS and Spaf swag? Read on!
CERIAS offices are moving in a matter of weeks. We don't want to have to box up everything, especially items we aren't likely to use any time soon (if ever) at the new location. Plus, some of these things are items we've heard people might like to have for themselves.
So.... We're going to give some of it away!
What's the catch? Well, we want to encourage people to do something good for others. And, as an institute (CERIAS) at a university (Purdue) and a life-long educator (Spaf), we thought that helping deserving students get cybersecurity education would be the way to do that.
To get some of the swag, as listed below, you need to make a donation to one of these charitable scholarships no later than August 5th, and provide proof of the donation and amount. We'll then package up your gifts and send them (we'll cover shipping inside the United States; if you are outside the U.S. we'll need to negotiate the shipping and any customs).
What charities? Only some of the best for cybersecurity students, and all established in memory of some pioneers in the field:
We'll note here that these are also worthwhile for regular donations. As non-profits, there may be tax advantages to your donations. And be sure to check if your employer has a matching donation program!
We have established the donation. What's the swag? While supplies last:



First, make a qualifying donation to one of the charities. Send proof of the donation, your address, and your shirt/hoodie/jacket size to: <spaf@cerias.purdue.edu>. You'll get the listed items while supplies last. If we run out of an item we will substitute an item of equal or better value.
| Minimum donation | Items shipped |
|---|---|
| $150 | 2 of Spaf's coffee mugs plus a CERIAS challenge coin |
| $200 | An additional item of CERIAS-branded merchandise plus 1 CERIAS mug |
| $300 | A copy of the book in addition to the above, plus an additional CERIAS item. | $500 | All of the above, plus 2 additional coffee mugs, plus a CERIAS logo fabric briefcase or portfolio. |
Remember, these are really all extra gifts. The real value is you making a donation to a worthwhile charity to help some deserving people study cybersecurity!
While cleaning out the storage closet we found a dozen remaining Spaf bobbleheads. This is the last of this collector's item! 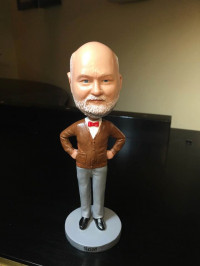 To get one, send us a check for a minimum of $100 made out to "Purdue University" with "Donation to CERIAS" on the memo line. (And, to be clear, Purdue University is also a non-profit entity.) Send the check with your return address to:
To get one, send us a check for a minimum of $100 made out to "Purdue University" with "Donation to CERIAS" on the memo line. (And, to be clear, Purdue University is also a non-profit entity.) Send the check with your return address to:
Bobblehead c/o Shawn Huddy
CERIAS -- Purdue University
656 Oval Drive
West Lafayette, IN 47907-2086