The Center for Education and Research in Information Assurance and Security (CERIAS)
The Center for Education and Research inInformation Assurance and Security (CERIAS)
 National Academy of Inventors names two Purdue faculty as 2024 fellows
National Academy of Inventors names two Purdue faculty as 2024 fellows
Two Purdue University faculty members, representing the College of Engineering and the College of Science, have been named fellows of the National Academy of Inventors, the organization announced Tuesday (Dec. 10). The 2024 fellow class represents 170 research universities and governmental and nonprofit research institutions worldwide. Edward Delp, the Charles William Harrison Distinguished Professor in the Elmore Family School of Electrical and Computer Engineering and professor of biomedical engineering, and Arun Ghosh, the Ian P. Rothwell Distinguished Professor of Chemistry and professor of medicinal chemistry and molecular pharmacology, will be inducted during NAI’s 14th annual meeting in June 2025 in Atlanta.
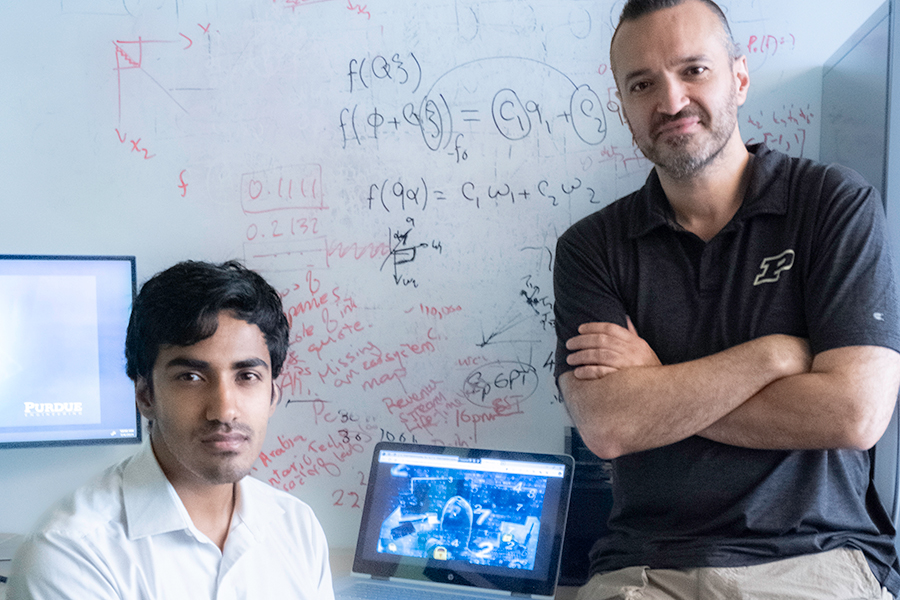
Aravind Machiry, assistant professor in the Elmore Family School of Electrical and Computer Engineering, has received an National Science Foundation (NSF) Faculty Early Career Development Program(CAREER) award for his proposed work titled “Securing Deeply Embedded Software.”
Saurabh Bagchi, professor in the Elmore Family School of Electrical and Computer Engineering, is a finalist for the Institution of Engineering Technology (IET) Achievement Medal, a global award in engineering. Winners will be announced and presented in London on Oct. 18.
Purdue Polytechnic professor Chad Laux has been awarded the International Book of the Year Award by the International Lean Six Sigma Institute (ILSSI) for his coauthored book, “Lean Sustainability: A Pathway to a Circular Economy.”
Gene Spafford joins HOU.SEC.CON founders Michael and Sam to chat about his start in cybersecurity and academia, his new book, and what to expect during his opening keynote at the conference.
 Purdue NE startup wins top tech prize from the Venture Club of Indiana
Purdue NE startup wins top tech prize from the Venture Club of Indiana
Earlier this month, Purdue-based startup Covert Defenses garnered the top prize of $10,000 in the digital tech category at the 2024 Innovation Showcase pitch competition hosted by the Venture Club of Indiana. Arvind Sundaram, co-founder and a Purdue alum (BSNE ’19, PhD NE ’22), pitched the patented self-healing Covert Cognizance platform to an audience of investors and budding entrepreneurs in Indiana’s successful startup ecosystem.
 Helping virtual cycling belong on the global stage
Helping virtual cycling belong on the global stage
CERIAS researchers help tackle cybersecurity issues to keep virtual cycling fair and secure.