Posts tagged php
Page Content
PHPSecInfo talk at OSCON 2008
If you’re at OSCON, and you love security, you may or may not enjoy my talk on PHPSecInfo, a security auditing tool for the PHP environment. I’m actually going to try to show some new code, so if you’ve seen it before, you can see it again – for the first time.
The talk is at 1:45pm Thursday, 07/24/2008.
The PHP App Insecurity Top 20
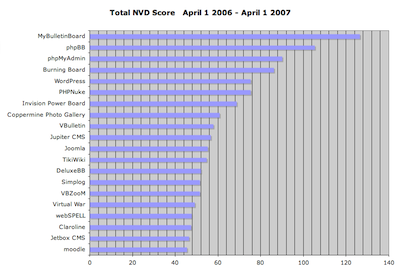
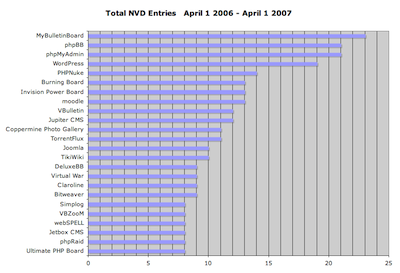
I’ve spent some of my down time in the past couple weeks working with the NIST NVD data to get stats on PHP application vulnerabilities. What follows is a breakdown of the 20 PHP-based applications that had the highest aggregate vulnerability scores (NIST assigns a score from 1-10 for the severity of each entry), and the highest total number of vulnerabilities, over the past 12 months. Of the two, I feel that the aggregate score is a better indicator of security issues.
A few caveats:
- The data here covers the period between April 1 2006 and April 1 2007.
- This obviously only includes reported vulnerabilities. There are surely a lot more applications that are very insecure, but for one reason or another haven’t had as many reports.
- I chose 20 as the cutoff mainly for the sake of making the data a little easier to swallow (and chart nicely). There are about 1,800 distinct apps in the NIST NVD that are (as far as I could determine) PHP-based.
Without further ado, here are the tepid Excel charts:
A couple notes:
- There are 25 entries in the top “20” by vulnerability count, due to matching vulnerability counts.
- I’d never even heard of MyBulletinBoard, the top entry in both lists. It hasn’t had any vulnerabilities in the NVD since September of 2006, which says something about how numerous and severe the entries between April and September 2006 were. This appears to be the same product as “MyBB,” so perhaps the situation has improved, as MyBB only has one NVD entry in the entire period (CVE-2007-0544).
- Wordpress has had a bad start to 2007, with numerous vulnerabilities that significantly increased its ranking. March 2007 was particularly bad, with 7 new vulnerabilities reported.
- Bulletin board/forum software is by far the most common type of application in the top 20. A couple forum apps that have very low numbers of vulnerability reports: Vanilla and FUDForum.
I do intend to keep this data up-to-date if people find it interesting, so let me know if you’d like me to do so, or if you’d like to see other types of analysis.
[tags]php, security, application security, vulnerabilities, nist, nvd, statistics[/tags]
PHPSecInfo v0.2 now available
The newest version of PHPSecInfo, version 0.2, is now available. Here are the major changes:
- Added link to “more info” in output. These lead to pages on the phpsec.org site giving more details on the test and what to do if you have a problem
- Modified CSS to improve readability and avoid license issue with PHP (the old CSS was derived from the output of
phpinfo()) - New test:
PhpSecInfo_Test_Session_Save_Path - Added display of “current” and “recommended” settings in test result output
- Various minor changes and bug fixes; see the CHANGELOG for details
-Download now
-Join the mailing list
Using mod_security to block PHP injection attacks
mod_security is an essential tool for securing any apache-based hosting environment. The Pathfinder High Performance Infrastructure blog has posted a good starter piece on using mod_security to block email injections.
One of the more common problems with PHP-based applications is that they can allow the injection of malicious content, such as SQL or email spam. In some cases we find that over 95% of a client’s ISP traffic is coming from spam injection. The solution? Grab an industrial size helping of Apache mod_security.
BTW, Ivan Ristic’s (the developer of mod_security) Web Security Blog is well worth a spot in your blogroll.
(Edit: fixed title. Duh.)