Archive
Results
Showing: 1 to 25 of 35Affiliation shown is the affiliation at the time the talk was given.
Beyond Separation of Duty: An Algebra for Specifying High-level Security Policies
Qihua Wang - Purdue University

Delving into differential privacy and anomaly detection: a meta-learning perspective
Yimin Chen - Virginia Tech
The Threat to Our Nation's Infrastructure and Intellectual Property Is Substantial
Dennis McCallam - Northrop Grumman

Pushing Computers to the Edge: Next Generation Security and Privacy Controls for Systems and IoT Devices
Ron Ross - National Institute for Standards and Technology (NIST)

Symposium Closing Keynote - Bits & Bytes, Flesh & Blood, and Adapting for the Next 20 Years
Josh Corman - PTC
Machine Learning Techniques for Anomaly Detection in Computer Security
Terran Lane - Purdue University
Multiple Independent Levels of Security Architecture: A High Robustness Approach Using COTS
Ben Calloni - Lockheed Martin
Secure Collaboration for Capacity Sharing in Logistics
Chris Clifton - Computer Science, Purdue University

Data, Privacy---and the Interactions Between Them
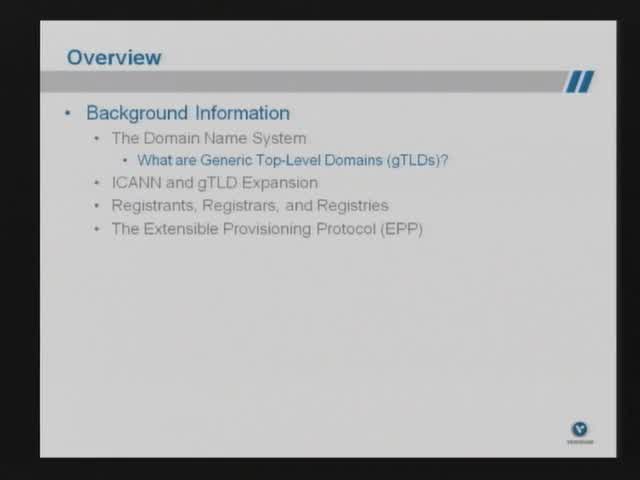
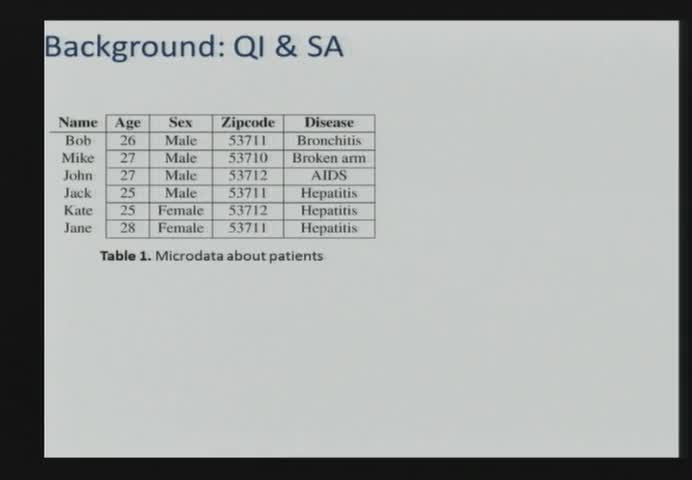
Christine Task - Knexus Research Corporation
Shifting focus: Aligning security with risk management
Jack Jones - Risk Management Insight
A Rules Based Statistical Algorithm for Keystroke Detection
Paul Kidwell - Purdue University
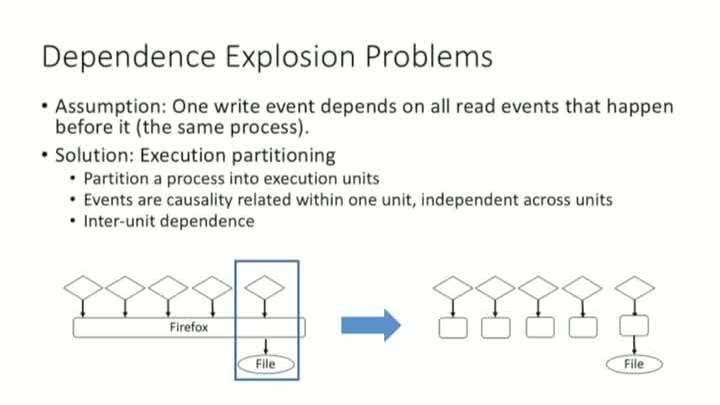
MPI: Multiple Perspective Attack Investigation with Semantic Aware Execution Partitioning
Shiqing Ma - Purdue University
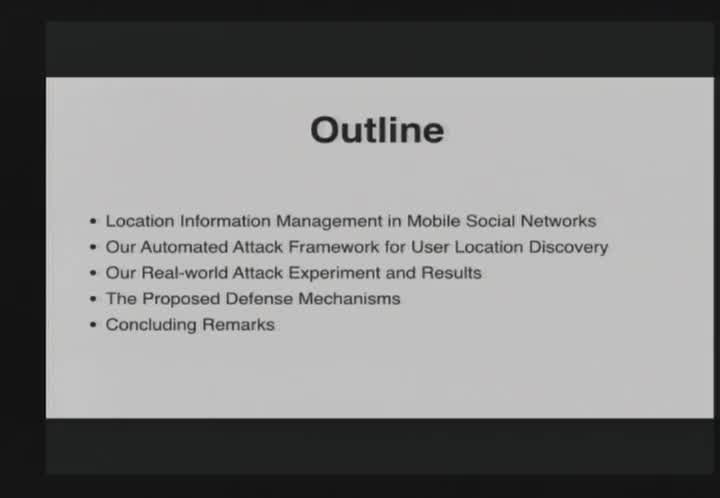
Breaking Mobile Social Networks for Automated User Location Tracking
Kui Ren - University at Buffalo

Problems and Challenges in Data Security Posture Management
Mummoorthy Murugesan - Normalyze, Inc.
Automatic Detection of Protocol Manipulation Attacks in Distributed Systems Implementations
Cristina Nita-Rotaru - Purdue University
Ways to Watch